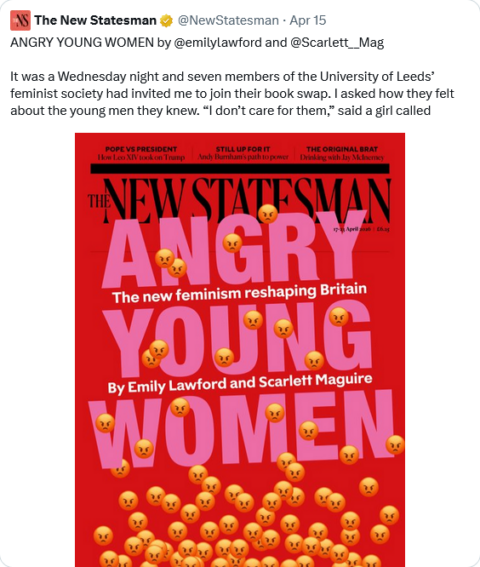
On the social media site formerly known as Twitter, Christian Heiens responds to a cover story in The New Statesman:
We were subjected to years of “young men are becoming radicalized, what’s driving this and how do we stop it?” discourse when in reality the typical young man saw practically zero change in his political outlook over the last 30 years.
The whole thing was one giant attempt to gaslight both young men and the public at large that they had suddenly moved well outside the Overton window and were either self-radicalizing or falling for extremist propaganda.
In reality, the problem was that young men were staying put rather than adopting increasingly radical progressive views. The real issue was that young women were flying off the rails, espousing views that would lead to the complete dissolution of civilization itself while acting like these were basic normal positions that completely sane people should hold.
That disconnect between what was being said and what was being done became so off kilter with reality that something finally began to break after 2020.
The problem isn’t with young men. The problem is that young women have gone certifiably insane. They’ve made radical progressivism their religion. They’re acting out on the perfectly healthy female tendency to act to uphold and preserve the existing social order.
Young women are trying to conserve an ideology they see as the stable bedrock of society, even if it’s actually an acidic collection of delusions that will inevitably destroy society itself. And they’re upset that young men aren’t doing what they see as their role to uphold that order as well.
In short, women are natural conservatives. They’re trying to conserve progressivism because it’s the reigning social order and theological governing system of Western civilization. And they’re upset and confused as to why young men aren’t stepping up to uphold it as well.
On Substack Notes, John Carter commented on the same New Republic The New Statesman cover story:
Women have never had it better than they do in modern Western countries. They are affluent, thanks to being given every advantage in education and employment; young women now hold more degrees, and make more money, than young men. They can marry whoever they want, from anywhere in the world, or they can marry no one at all. They can sleep with whoever they want, with however many people they want, with no risk of pregnancy, and if they get the ick later they can decide that it was rape and their abuser will be punished. Any opposition to their cultural or political preferences is automatically classified as hate, and every institution acts to denounce and punish this unacceptable hatred on their behalf … in no small part because they have taken over these institutions.
Women have never had it better, and they are absolutely incandescent with fury about that.