We adopt many web services because they’re convenient (and free!), but it’s only after becoming dependent on those services that we recognize why they were provided for free in the first place: after all, it’s only by eliminating the inconvenience of paying users that startups can snag attention and secure the freedom to alter, downgrade, or cancel their services at will. By then, of course, we’re trapped in an unstable relationship, and our only means of recourse is to wail as loudly as possible, “You broke my heart!”
The big lesson that should have come out of the Tumbleocalypse was that we trust too easily. Did any of us listen? Nah. Instead, we’re signing our friends up to Dropbox to score 250 megs of bonus storage space and sending our most important documents to “the cloud.” We trust Dropbox because we trust others who use Dropbox: web designers, tech writers and professionals who, we believe, would never gamble with an unproven, flaky, or suspect service. Without this kind of trust-by-proxy, free web services couldn’t survive at all. Can you imagine anybody in their right mind signing up for a Facebook account today without a good friend by the sidelines whispering, “Don’t mind all that privacy whaffle. I know these guys mean well.”
Cloud storage is convenient, of course — ask anybody who’s experienced the horrors of manually synching PC to iPhone — but we downplay the risks involved in outsourcing control of the data we own. We so badly want to live in the future that we’ve lost the ability to question what living in the future might actually mean.
[. . .]
Those who believe that “the cloud” can act as a storage platform for our collective memories believe that everything that was available to us yesterday will be just as available to us tomorrow. Where exactly does this conviction come from?
The web is like any other sprawling city, and maybe worse: it’s so damn rickety it’s a minor miracle it hasn’t collapsed entirely. When you link, you do so trusting that the data to which you direct your readers won’t just up and disappear into the virtual ether. Except that, inevitably, it will — the short history of the web has established that much. We live somewhere, we leave, it becomes forgotten, and then we come back years later to find our old haunts brutally 404’d.
Connor O’Brien, “Link Rot”, The Bygone Bureau, 2011-01-17
January 17, 2011
QotD: The impermanence of “The Cloud”
Another sexting case, with a slightly misleading headline
A brief report at the National Post implies something a bit different than the article actually says: Woman jailed after nude photo posted on Facebook.
Eighteen-year-old Angelica Nicholson of Portage, Ind. sent a nude photo of herself to a “male acquaintance” — apparently to the displeasure of the acquaintance’s girlfriend.
The girlfriend in turn posted the photo on Facebook and after an exchange of heated text messaging, Ms. Nicholson contacted Facebook to remove the photo.
Dissatisfied with Facebook’s response time, Ms. Nicholson called 911 and claimed she was 17 to get the photo removed faster.
Police found out the woman was 18 from government records, and Ms. Nicholson was arrested for false reporting.
So, yes, she was arrested, but not for posting a nude photo on Facebook. Abusing 911 services, yes, but not for posting to Facebook.
January 15, 2011
Indian model photoshopped against her will
It’s no secret that most of the images used for magazine covers have had a healthy dose of Photoshoppery, but this is a few filters too far:

Leave it to ELLE Magazine to photochop the world’s most beautiful woman. Aishwarya Rai, the reigning queen of Indian cinema, model and classically trained dancer is currently on the cover of ELLE India — several shades lighter. Rai’s skin has been lightened and her dark brown hair appears to have a red tint to it.
The Times of India reported the former Miss World is “furious with the bleaching botch-up” and is considering taking legal action against ELLE.
ELLE’s mission is to make women “chic and smart, guide their self-expression, and encourage their personal power,” but their recent covers could lead readers to believe that “chic, smart and personal empowerment” only comes to those with light skin.
H/T to Tim Harford for the link.
What do you do when you find something cool on the Internet?
If you’re cool, you do something like this:
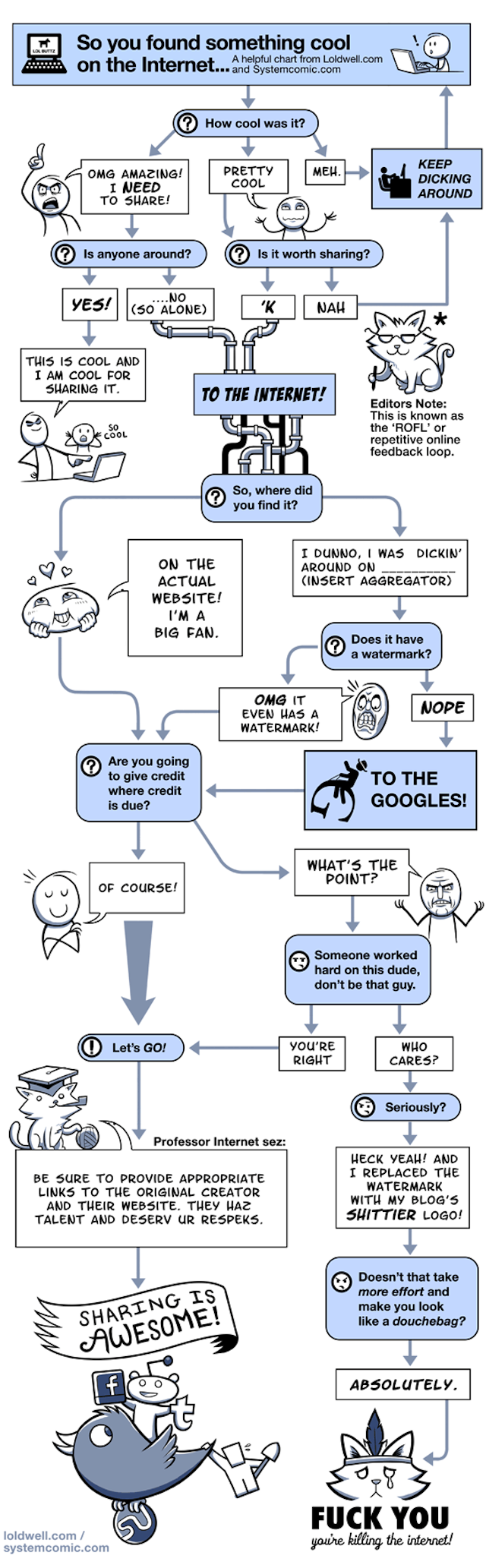
Original work by Caldy and Rosscott. H/T to Royce McDaniels for bringing it to my attention.
Remember, kids, everytime you re-use someone’s creative work on the Internet without giving credit, God (or your Deity of choice) kills a kitten. Don’t make God (or your Deity of choice) kill any more kittens!
January 14, 2011
Last year’s biggest military developments
Strategy Page lists some of the most significant military developments of 2010:
* Infantry. Here we saw more evolution, not revolution, in infantry gear. But at least the trends continued to move in the right direction. The biggest change is the equipment that must be carried. Until the 1980s, you could strip down (for actual fighting) to your helmet, weapon (assault rifle and knife), ammo (hanging from webbing on your chest, along with grenades), canteen and first aid kit (on your belt) and your combat uniform. Total load was 13-14 kg (about 30 pounds). You could move freely, and quickly, like this, and you quickly found that speed and agility was a lifesaver in combat. But now the minimum load carried is twice as much (27 kg), and, worse yet, more restrictive. Over the last seven years, this has translated into some dramatic changes in training. In Iraq, troops found they were not in the best condition to run around with all that weight. This was worse in Afghanistan, with all those hills. Plus, the vest constricted movement, and that took time to adjust to. Commanders complained about troops not being properly trained, and that led to a series of changes in basic and unit training. The big change in basic was to condition troops to handle the heavy weights they would be carrying, for extended periods of time. This was particularly critical for non-combat troops (especially those operating convoys) outside of camps (where you usually didn’t have to wear armor and combat gear.) New exercises were developed. Infantry troops got several months of additional training after basic, and had plenty of opportunity to adjust to moving around wearing 14 kg or more of gear. The heavier weight included better armor and equipment (night vision, personal radio, weapon sights), which reduced combat deaths, and made the troops more lethal. But now the troops accept the fact that a lot of essential training takes place in the gym, particularly the weight room. The army and marines have been developing lighter and more comfortable versions of essential gear, but there’s still a need for muscle. This decade of infantry innovation has been noted by other armies around the world, and they are all hustling to emulate this American revolution. Not just to get the gadgets, but to implement the new training methods as well.
* Support. Few pay attention to support functions, especially no one in the media. But here is where big things happen. One of things has been how video games joined the army. Over the last eight years, billions of dollars has been spent on creating several generations of increasingly accurate combat simulators for training troops to deal with roadside bombs, hostile civilians, flying UAVs and new enemy tactics. These sims are taken for granted inside the army and marines, but still seem out of place to ill informed outsiders.
[. . .]
* Naval Power. The U.S. Navy has accepted the fact that is has gotten smaller, and that this process will continue. The navy shrunk by 20 percent in the last decade, to a force of 280 ships. The main reason is the high cost of new ships, to replace those that are wearing out and being retired. In the next decade, the fleet is expected to shrink another 20 percent, again because Congress refuses to provide enough money to replace older ships (only about $14 billion a year, at most, is provided for new ships, and this is expected to shrink.) New ships cost, on average, $2.5 billion each. This is made possible because of six billion dollar destroyers, seven billion dollar subs and eleven billion dollar carriers. This is offset somewhat by $1.7 billion amphibious ships and half billion dollar LCS (a compact, controversial, ship design). The big news is that the admirals are actively brainstorming how to live with a high cost/low income future, not try to magically make it go away.
January 13, 2011
Adobe finally gets the message
Ever wanted to delete all the tracking cookies that your browser collects? Most browsers provide ways to do that for ordinary cookies, but did nothing for the Flash cookies. Adobe seems to have heard the demands to fix this:
Adobe has finally fixed a privacy weakness that threatened users of its ubiquitous Flash Player: the software’s storing of cookie-like files that many websites used to track visitors’ behavior against their wishes.
So-called LSOs, or local shared objects, are useful for storing user preferences, such as the preferred sound volume when visiting YouTube, but the Flash feature comes with a dark side. Unscrupulous websites can use them to restore tracking cookies even after a user deliberately deletes them. Files that do this have come to be known as Flash cookies.
Now, developers at Adobe have worked with their counterparts at Mozilla and Google on a programming interface that allows LSOs to be deleted from within the settings panel of compliant browsers. The API, known as NPAPI ClearSiteData, has already been approved for implementation in Firefox. It will soon appear on the Google Chrome dev channel.
January 11, 2011
Glass that is “stronger than steel” developed
Arnie Bruce-Cooper reports on a recent development in high-strength glass:
In the world of materials, strength (the amount of force a substance can withstand) and toughness (its capacity to resist fracturing) are not merely different attributes; they’re very difficult to achieve together. Now a collaboration of researchers from Caltech and the Department of Energy’s Lawrence Berkeley National Laboratory has created a form of glass that has both qualities. It’s stronger and tougher than steel or, indeed, any other known material. The material features palladium, a metal whose possible use in glasses was recognized 45 years ago.
[. . .]
The work is outlined in a study published this week in the journal Nature Materials. Marios Demetriou, a professor at Caltech and lead author of the paper, says the work involved finding a particularly strong version of the simplest form of glass, called marginal glass, and then turning it into the even stronger form known as bulk glass.
“What we did here is find a very, very tough marginal glass made of palladium with small fractions of metalloids like phosphorus, silicon, and germanium, which yielded one-millimeter-thick samples. And we just said, let’s add very little of something that will make it bulk without making it brittle,” says Demetriou. By adding 3.5 percent silver to this marginal glass, Demetriou was able to increase the thickness to six millimeters while maintaining its toughness.
H/T to Virginia Postrel for the link.
January 10, 2011
QotD: Geeks and Hackers defined
One of the interesting things about being a participant-observer anthropologist, as I am, is that you often develop implicit knowledge that doesn’t become explicit until someone challenges you on it. The seed of this post was on a recent comment thread where I was challenged to specify the difference between a geek and a hacker. And I found that I knew the answer. Geeks are consumers of culture; hackers are producers.
Thus, one doesn’t expect a “gaming geek” or a “computer geek” or a “physics geek” to actually produce games or software or original physics — but a “computer hacker” is expected to produce software, or (less commonly) hardware customizations or homebrewing. I cannot attest to the use of the terms “gaming hacker” or “physics hacker”, but I am as certain as of what I had for breakfast that computer hackers would expect a person so labeled to originate games or physics rather than merely being a connoisseur of such things.
[. . .]
All hackers are, almost by definition, geeks — but the reverse is not true.
Eric S. Raymond, “Geeks, hackers, nerds, and crackers: on language boundaries”, Armed and Dangerous, 2011-01-09
Facebook has a repeat of their earlier boob
Facebook apparently has something against breasts — specifically those used to feed babies:
Facebook had one of its nipple-related related brainstorms last week, banning, unbanning, then re-banning breastfeeding support group, The Leaky Boob.
The Leaky Boob group allows almost 11,000 mothers to share their experiences on breastfeeding — as well as providing casual visitors with a treasure trove of advice and tips. Well, it would do, if Facebook didn’t keep deleting it — as they did the previous weekend.
This provoked an angry reaction from the tens of thousands of women who use the page for information and support.
Breastfeeding supporters responded swiftly, creating two pages on Facebook, Bring Back the Leaky Boob and TLB Support, which gained the best part of 10,000 fans in just two days.
On Tuesday, according to group founder Jessica Martin-Weber, the page was back up.
On Wednesday it was gone again.
Then, later in the day, it returned and is still up today.
It’s easy to see how the content of TLB might be offensive to closed-minded people, and if the banning mechanism Facebook uses is mostly automated, it’d explain the way in which the group was originally banned. If all it takes is a complaint, and the (I assume automated) follow-up to the complaint only checks for certain things, the first shutdown is explained. The fact that the group has been through this process before shows a weakness in Facebook’s administrative tracking policies.
December 30, 2010
Font geek humour
How geeky do you have to be to find this sort of thing funny as hell?
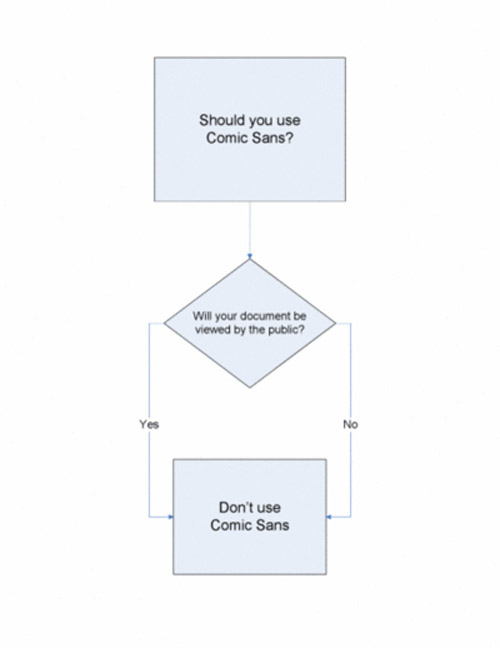
H/T to Eric S. Raymond for the link.
December 21, 2010
EMALs successfully launches aircraft
In what must be welcome news for naval aviators, the next-generation catapult for launching aircraft from carriers was successful in a land-based test:
The US Navy says it has successfully launched a jet fighter into flight using a radical new electromagnetically powered catapult. The feat is important for the Americans, whose next supercarrier will be a disastrous botch without the new tech: it is even more critical for the future of the Royal Navy.
The US Naval Air Systems Command (NAVAIR) announced the test success of its Electromagnetic Aircraft Launch System (EMALS) last night, saying that the shore-based trials catapult at Lakehurst, New Jersey, successfully launched a Navy F/A-18E Super Hornet on Saturday.
“I thought the launch went great,” said Lieutenant Daniel Radocaj, the test pilot who flew the Hornet off the electric mass-driver. “I got excited once I was on the catapult but I went through the same procedures as on a steam catapult. The catapult stroke felt similar to a steam catapult and EMALS met all of the expectations I had.”
The timing of the test is crucial for the US Navy’s next big warship:
The next US fleet carrier — CVN 78, aka USS Gerald R Ford — is now at an advanced stage of build, and was designed around the EMALS. If EMALS couldn’t be made to work, the US Navy would have found itself in possession of the world’s biggest helicopter carrier. There will be much celebration at NAVAIR following Saturday’s success.
The next step in robotics: combat casualty recovery bots
It’s not ready to be used in the field yet, but the next military robot may be a stretcher bearer:
Killing a soldier removes one enemy from the fray. Wounding him removes three: the victim and the two who have to carry him from the field of battle. That cynical calculation lies behind the design of many weapons that are intended to incapacitate rather than annihilate. But robotics may change the equation.
The Battlefield Extraction-Assist Robot, BEAR for short, is, in the words of Gary Gilbert of the American Army’s Telemedicine and Advanced Technology Research Centre (TATRC), “a highly agile and powerful mobile robot capable of lifting and carrying a combat casualty from a hazardous area across uneven terrain.” On top of that, when it is not saving lives, it can perform difficult, heavy and repetitive tasks, such as the loading and unloading of ammunition.
The current prototype BEAR is a small, tracked vehicle with two hydraulic arms and a set of video cameras that provide a view of its surroundings to its operator across a wireless link. It has been developed by TATRC in collaboration with Vecna Technologies, a company based in Maryland that invented the robot.
December 18, 2010
Man bites dog story, military style
In Afghanistan and Iraq, they are finding uses for manned aircraft to supplement Predator UAV patrols:
The U.S. Air Force MC-12 “manned UAV replacement” has been in Afghanistan for a year, and has proved successful. This despite the fact that it can only stay in action for seven hours per sortie, versus more than twice the hours for a UAV. But the military needs more UAV capabilities (vidcams overhead for hours at a time), and doesn’t care if the pilots are in the air or on the ground.
[. . .]
The MC-12 is basically a militarized version of the Beech King Air. The army began using the Beech aircraft as the RC-12 in the 1970s, and has been seeking a replacement for the last few years. But then it was realized that the RC-12 was suitable for use as a Predator substitute.
The King Air 350 is a 5.6 ton, twin engine aircraft. The MC-12 can stay in the air for up to eight hours per sortie. Not quite what the Predator can do (over 20 hours per sortie), but good enough to help meet the demand. The MC-12 has advantages over UAVs. It can carry over a ton of sensors, several times what a Predator can haul. The MC-12 can fly higher (11 kilometers/35,000 feet) and is faster (over 500 kilometers an hour, versus 215 for the Predator.) The MC-12s cost about $20 million each, more than twice what a Predator goes for. The MC-12’s crew consists of two pilots and two equipment operators. Some of the sensors are operated from the ground.



