May 1, 2012
The Onion: Every Potential 2040 President Already Unelectable Due To Facebook
April 30, 2012
Twitter’s “Red Guard” of flag-spam abusers
Some nasty tricks being played by some Twitter users, abusing the report feature that is supposed to help cut down on spam posts to attempt to shut down opinions they find offensive:
Shortly after their video “If I Wanted America to Fail” went viral, Free Market America found themselves kicked off Twitter, a popular social media resource that allows users to post very short messages. After a few hours of confusion, their account was reinstated.
This past Sunday, the Twitter account of Chris Loesch, husband of conservative pundit Dana Loesch, was abruptly shut down. After a massive outcry, and the creation of a Twitter topic called “#FreeChrisLoesch” that swiftly became one of the hottest “hash tags” on the network, Chris’ account was reactivated… for a couple of hours. By Monday morning, he was gone again, after his account was restored and removed several more times.
What did Free Market America and Chris Loesch do to warrant suspension? After all, people like Spike Lee and Roseanne Barr flagrantly, openly, defiantly violated Twitter’s terms of service, and put human lives in jeopardy, by distributing personal information about George Zimmerman, the shooter in the Trayvon Martin case. Their accounts have not been suspended. What violation of Loesch’s compares to using Twitter to target someone for assault by an angry mob — and, for that matter, sending the mob to the wrong address?
These suspensions were apparently the work of “flag spammers,” digital brown shirt gangs that make coordinated attacks to silence conservative voices by abusing Twitter’s spam flagging feature. Al Gore coined the term “digital brown shirts” to describe the online squadrons supposedly unleashed to “harass and hector any journalist who is critical of the President.” Of course, he was talking about President Bush, and there weren’t any actual “digital brown shirts” at the time, but this is precisely the sort of behavior he was describing.
The F-35, the “supersonic albatross”?
Foreign Policy has a feature up called “The Jet That Ate the Pentagon” by Winslow Wheeler:
The United States is making a gigantic investment in the F-35 Joint Strike Fighter, billed by its advocates as the next — by their count the fifth — generation of air-to-air and air-to-ground combat aircraft. Claimed to be near invisible to radar and able to dominate any future battlefield, the F-35 will replace most of the air-combat aircraft in the inventories of the U.S. Air Force, Navy, Marine Corps, and at least nine foreign allies, and it will be in those inventories for the next 55 years. It’s no secret, however, that the program — the most expensive in American history — is a calamity.
[. . .]
How bad is it? A review of the F-35’s cost, schedule, and performance — three essential measures of any Pentagon program — shows the problems are fundamental and still growing.
First, with regard to cost — a particularly important factor in what politicians keep saying is an austere defense budget environment — the F-35 is simply unaffordable. Although the plane was originally billed as a low-cost solution, major cost increases have plagued the program throughout the last decade. Last year, Pentagon leadership told Congress the acquisition price had increased another 16 percent, from $328.3 billion to $379.4 billion for the 2,457 aircraft to be bought. Not to worry, however — they pledged to finally reverse the growth.
The result? This February, the price increased another 4 percent to $395.7 billion and then even further in April. Don’t expect the cost overruns to end there: The test program is only 20 percent complete, the Government Accountability Office has reported, and the toughest tests are yet to come. Overall, the program’s cost has grown 75 percent from its original 2001 estimate of $226.5 billion — and that was for a larger buy of 2,866 aircraft.
At those prices, there are few allies who will be able to afford them — Canada clearly not among them.
April 28, 2012
The eternal problem of “sea blindness”
Unlike armies which used to be raised at the drop of a hat (relatively speaking), navies have always been slower to grow at times of need. To build an army in the pre-nuclear age, you called up all your young men, gave them the absolute minimum of training and there’s your army. It might not be particularly capable, but an army it was. You could call up as many men as you liked for your navy, but without the ships and a significantly larger proportion of trained officers and petty officers, you don’t have a navy.
Navies take time to build, and in peacetime few nations are willing to support the kind of naval establishment they may need in wartime. Sir Humphrey at the Thin Pinstriped Line discusses this age-long phenomenon of “sea blindness”:
The first question that comes to mind is ‘what is Sea Blindness’? Arguably it simply means that the public, and by extension Governments of nations do not understand the maritime domain, and do not understand the case for the maritime domain – not just from a military, but also from a wider sector perspective. Personally this author dislikes this term, as it implies a state of permanence towards the public view of the sea. The phrase implies that there is no cure to the notion that the public will never understand the maritime case, and that instead it is the role of senior leaders in the maritime community to act as guides or aids to a public which will never understand the importance of maritime power.
The next question is surely, has the public ever not been sea blind? Arguably since time immemorial the public have been unwilling to support the long term interests of the maritime case – one can only look back through history at the maritime wars fought by the UK, and other nations, and see cases of weak defences needing bolstering at a desperate hour. Conversely, the major combat indicator of a potential threat has often come through the augmenting or enhancing of fleets in other nations. It is rare through history to find examples of nations maintaining powerful fleets in a state of permanent existence – rather it is the case that great fleets are maintained only for the duration of a crisis and thereafter disposed of. Simply look to the case of the Royal Navy after the Napoleonic Wars, where the manpower was disposed of and ships returned to the Reserve. It seems fair to argue that the public have no interest in funding a great fleet when there is no threat – the demands on their pockets are simply too great to bear.
[. . .]
More broadly, this author would argue that ‘Sea Blindness’ when it comes to understanding the maritime domain is not a new condition – people have historically not understood the dependency that humanity has on the sea. In reality, although the UK is an island, very few people relatively speaking actively involve themselves in maritime matters. Outside of the small fishing / trading community, or those who work in the maritime support sector, it is probably fair to argue that most people simply don’t have the professional links to see the sea for what it is – an essential gateway to prosperity and survival. But then again, one could make the argument that few people really investigate or seek to understand the many different networks, links or dependencies that nations have on all manner of objects, trade and supplies. It’s likely that few people in the UK knew that the IT industry was reliant on factories in Thailand to make hard drives until the floods damaged production and prices soared. Similarly the automobile industry is struggling after a fire in a factory in Germany shut down production of resin, reducing the ability to make cars globally. The reality is that we live in an interdependent world on many fronts, but it is so complicated, and so networked that it is almost too difficult to follow.
April 20, 2012
Building High Speed Rail won’t do much to cut carbon dioxide emissions
Brad Plumer at the Washington Post on the latest straw that high speed rail enthusiasts have been grabbing to justify their expensive toys:
… Brown’s administration has proposed using money raised by California’s new climate law. Under the state’s cap-and-trade system for carbon emissions, power plants and factories will have to buy permits to pollute. Brown has suggested diverting this money into high-speed rail. But there are two problems here. For one, this might be illegal, as the state’s Legislative Analyst’s Office concluded on Tuesday. But second — and more broadly — high-speed rail turns out not to be the most effective use of money that’s meant to combat global warming.
Paul Druce at Reason & Rail offered up a few numbers on this topic last year. The California High Speed Rail Authority claims that by 2030, if the train ran entirely on renewable energy, then it would reduce the state’s carbon emissions by about 5.4 million metric tons a year. If you ignore all the energy used to build the system, that means the rail network would reduce California’s emissions at a cost of $12,506 per metric ton of carbon dioxide.
That’s a pricey way to cut carbon. To put this in perspective, research has suggested that you could plant 100 million acres of trees and reforest the United States for a cost of about $21 to $91 per ton of carbon dioxide. Alternatively, a study by Dan Kammen of UC Berkeley found that it would cost somewhere between $59 and $87 per ton of carbon dioxide to phase out coal power in the Western United States and replace it with solar, wind and geothermal. If reducing greenhouse gases is your goal, then there are much more cost-effective ways to do it than building a bullet train.
April 19, 2012
“Ontario is on track to have the highest electricity prices … in North America”
Scott Stinson explains why Ontario consumers are facing huge price hikes for electricity over the next 18 months:
It’s no secret that Dalton McGuinty’s Liberals have placed a huge bet on growing a green-energy sector by subsidizing the production of renewable energy. Although energy bills have been steadily rising since the party took power in 2003 — the average cost of a kilowatt of electricity was more than 30% higher last year than it was five years ago — the Liberals have somewhat masked this fact by handing a 10% rebate back to consumers with the euphemistically named Clean Energy Benefit, which also happens to utterly contradict the conservation incentive that should be part of a switch to a greener grid.
Electricity costs, though, are set to spike.
“Ontario’s power system is fuelled by consumers to the tune of about $16-billion a year,” says Tom Adams, an energy consultant who has written extensively on electricity and environmental issues. “That number is headed for $23-billion or $24-billion soon, by 2016,” he says in an interview.
[. . .]
Mr. Adams notes that when the Green Energy Act, with its guarantees of above-market rates for wind and solar electricity known as feed-in-tariffs (FIT), was introduced in 2009, the Liberals said electricity costs would only be impacted by about 1% annually. We now know that rates for consumers are rising by 9% a year. “The government says about half of that is due to Green Energy, but if they were being honest it would be more than that,” Mr. Adams says.
The coming increases, meanwhile, which can partly be attributed to locked-in contracts for renewable energy, are also a result of a host of other factors, from new generation capacity being introduced to phase-out costs of existing facilities to new transmission capacity being added to the energy grid.
April 17, 2012
SpaceX Dragon cleared for April 30 flight to ISS
Brid-Aine Parnell updates the status of the SpaceX Dragon re-supply flight to the International Space Station at the end of the month:
The cargoship test flight, assuming it goes off without a hitch, will mark the first time a commercially made spacecraft has ever blasted off to visit the ISS.
NASA and SpaceX officials met yesterday in Houston for the Flight Readiness Review, a typical part of pre-launch prep at the agency, and confirmed that the Dragon and its SpaceX Falcon 9 rocket were on track for the end of this month.
“Everything looks good heading to the April 30 launch date,” said Bill Gerstenmaier, NASA’s associate administrator for Human Exploration and Operations, in a canned statement.
The Dragon is due to blast off from Cape Canaveral at 12.22 EDT (16.22 GMT) carrying 1,200 pounds of cargo.
Because this is a test flight, the cargo isn’t critical stuff for the astronauts, but NASA and SpaceX are still hoping to see the ship fly close enough to the station for its robotic arm to grab it and berth it, which is the tricky bit.
April 16, 2012
“This sort of investment pays for itself ten-fold over a very short period of time”
You see? This is what’s wrong with private enterprise, especially in California. Those wimps aren’t willing to invest in something that will “pay for itself” ten times over in a “very short period of time”. That’s why all the greatest economic advances have come from over-aged students, business council speechifiers, bureaucrats, and career apparatchiks!
If you believe calling your opponents names is a sign that you have lost the argument, then this new high-speed rail commercial from the California Alliance for Jobs — in which unexpectedly macho proponents of the
$41 billion,$110 billion,$98.5 billion, $68.4 billion high-speed rail project deride skeptics as “wimps” — is pretty much the end of the line […]What reveals the intellectual bankruptcy of the high-speed rail project is not the insults but that what is supposed to be a rousing propaganda piece comes off like an orientation video for new hires at a failing company.
The video’s cast includes
hacksrespected citizens from Operating Engineers Local 3, including Alliance for Jobs Executive Director Jim Earp, along with leaders from what’s usually referred to as the “business community” whose skill sets cluster around serving on business councils rather than doing any actual business. There’s also a career apparatchik and the founder of the “I Will Ride” Student Coalition, who is apparently a UC Merced senior but looks at least a decade too old.[. . .]
Again, why not just claim the Fresno-Bakersfield line will end up carrying 38 million people, the entire population of California, every day? It would be no less accurate than the current claims, which have been made with no data on ticket costs, no comparative studies of existing bullet-train ridership, or anything else that can reasonably pass for due diligence.
Oh, and nobody actually knows where the bullet train will go to or from. (Past, present and possibly future candidates include Corcoran, Borden, Fresno, Anaheim, Los Angeles, San Francisco, and some guy named Dave’s rec room.) You wouldn’t build a patio with the amount of planning that’s gone into the high-speed rail project.
To put the headline into a bit of perspective, note that only one high speed rail line in the world is profitable. This is an old hobby horse of mine and I’ve posted about High Speed Railways a few times before.
Update: And to answer the question about why parts of Europe, Japan, and China have high speed rail systems and neither Canada nor the United States do, here’s a brief overview I wrote last year:
The best place to build a high speed rail system for the US would be the Boston-New York-Washington corridor (aka “Bosnywash”, for the assumed urban agglomeration that would occur as the cities reach toward one another). It has the necessary population density to potentially turn an HSR system into a practical, possibly even profitable, part of the transportation solution. The problem is that without an enormous eminent domain land-grab to cheat every land-owner of the fair value of their property, it just can’t be done. Buying enough contiguous sections of land to connect these cities would be so expensive that scrapping and replacing the entire navy every year would be a bargain in comparison.
The American railway system is built around freight: passenger traffic is a tiny sliver of the whole picture. Ordinary passenger trains cause traffic and scheduling difficulties because they travel at higher speeds, but require more frequent stops than freight trains, and their schedules have to be adjusted to passenger needs (passenger traffic peaks early to mid-morning and early to mid-evening). The frequency of passenger trains can “crowd out” the freight traffic the railway actually earns money on.
Most railway companies prefer to avoid having the complications of carrying passengers at all — that’s why Amtrak (and VIA Rail in Canada) was set up in the first place, to take the burden of money-losing passenger services off the shoulders of deeply indebted railways. Even after the new entity lopped off huge numbers of passenger trains from its schedule, it couldn’t turn a profit on the scaled-down services it was offering.
Ordinary passenger trains can, at a stretch, share rail with freight traffic, but high speed trains cannot. At higher speeds, the actual construction of the track has to change to deal with the physical problem of safely guiding the fast passenger trains along the rail. Signalling must also change to suit the far-higher speeds — and the matching far-longer safe braking distances. High speed rail lines cannot be interrupted with grade crossings, for the safety of passengers and bystanders, so additional bridges and tunnels must be built to avoid bringing road vehicles and pedestrians too close to the trains.
In other words, a high speed railway line is far from being just a faster version of what we already have: it would have to be built separately, to much higher standards of construction.
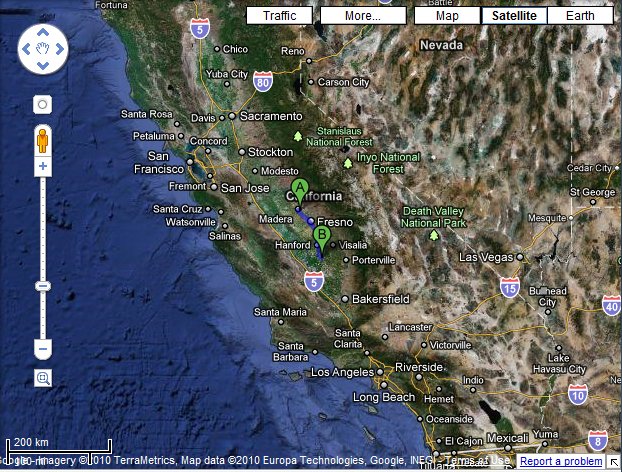
Getting back to the California HSR line; it goes from A to B on this map:
Okay, you think, at least Fresno will get some snazzy slick rail service . . . except this section will be built but not operated until further connecting sections are built . . . at a later date. Maybe. It will be the track, including elevated sections through Fresno, and the physical right-of-way, but no electrical system to power the trains; but that’s fine, because the budget doesn’t include any actual trains.
India’s long, twisting path to nuclear submarine capabilities
India would like to run their own nuclear-powered submarines, but it’s taken longer for them to achieve that than they’d hoped:
On April 4th the new Russian Akula II SSN (nuclear attack submarine) Nerpa, that was supposed to be delivered to India (which is leasing it) two years ago, was finally turned over. It’s worse than it sounds. Three years ago, during sea trials there was an equipment failure on Nerpa that killed 20 sailors and shipyard workers. This delayed sea trials for many months and the Russians found more items that needed attention. These additional inspections and repairs continued until quite recently.
[. . .]
Indian money enabled Russia to complete construction on at least two Akulas that were less than half finished at the end of the Cold War. This was another aftereffect of the collapse of the Soviet Union. Several major shipbuilding projects were basically put on hold (which still cost a lot of money) in the hopes that something would turn up. In this case, it was Indians with lots of cash. But money could not overcome the construction problems and poor design decisions the Russians made. The single Akula II India was leasing was delayed again and again. The 8,100 ton Akula II has a crew of 73. The one leased by India has eight 533mm (21 inch) torpedo tubes and 40 torpedoes.
Meanwhile, in 2009, India launched its first nuclear submarine, the INS Arihant (Destroyer of Enemies). This came after over a decade of planning and construction. What was not revealed at the times was that the Arihant was launched without its nuclear reactor, which was not installed until 2011. Arihant is supposed to be ready for service later this year.
April 15, 2012
Virginia county considering creating first virtual public high school
In many ways, it’s a tribute to the resilience and determination of the educational establishment that it’s taken this long for a school district to even consider offering completely online classes:
Fairfax County schools could become the first in the Washington region to create a virtual public high school that would allow students to take all their classes from a computer at home.
No sports teams. No pep rallies. No lockers, no hall passes. Instead, assignments delivered on-screen and after-school clubs that meet online.
It’s a reimagination of the American high school experience. And it’s a nod to the power of the school choice movement, which has given rise to the widespread expectation that parents should have a menu of options to customize their children’s education.
Of course, it might not just be simple willingness to allow more choice on the part of the school district … there might be other pressures being applied:
Dozens of younger students have left Fairfax schools for the public Virginia Virtual Academy, the first statewide full-time virtual program. Open to any Virginia student in kindergarten through eighth grade, it is run by a Herndon firm — K12 Inc., the nation’s largest operator of public virtual schools — and enrolls nearly 500 students.
April 14, 2012
April 11, 2012
“Facebook is like an NYPD police van crashing into an IKEA, forever”
An interesting analysis of the Instagram takeover by Facebook:
First, to understand this deal it’s important to understand Facebook. Unfortunately everything about Facebook defies logic. In terms of user experience (insider jargon: “UX”), Facebook is like an NYPD police van crashing into an IKEA, forever — a chaotic mess of products designed to burrow into every facet of your life. The company is also technologically weird. For example, much of the code that runs the site is written in a horrible computer language called PHP, which stands for nothing you care about. Millions of websites are built with PHP, because it works and it’s cheap to run, but PHP is a programming language like scrapple is a meat. Imagine eating two pounds of scrapple every day for the rest of your life — that’s what Facebook does, programming-wise. Which is just to say that Facebook has its own way of doing things that looks very suspect from the outside world — but man, does it work.
Now consider Instagram. If Facebook is a sprawling, intertextual garden of forking pokes, Instagram is no more complex than a chapbook of poetry: It lets you share pictures with your friends and keep track of strangers who post interesting pictures. It barely has a website; all the action happens on mobile devices. Thirty million people use it to pass time in the bathroom. You can add some fairly silly filters to the photos to make the pictures look like they were taken in the seventies, but that’s more of a novelty than a requirement. So that’s Instagram. It’s not a site, or an app. What it is, really, is a product.
[. . .]
To some users, this looks like a sellout. And that’s because it is. You might think the people crabbing about how Instagram is going to suck now are just being naïve, but I don’t think that’s true. Small product companies put forth that the user is a sacred being, and that community is all-important. That the money to pay for the service comes from venture capital, which seeks a specific return on investment over a period of time, is between the company and the venture capitalists; the relationship between the user and the product is holy, or is supposed to be.
So if you’re an Instagram user, you’ve been picking up on all of the cues about how important you are, how valuable you are to Instagram. Then along comes Facebook, the great alien presence that just hovers over our cities, year after year, as we wait and fear. You turn on the television and there it is, right above the Empire State Building, humming. And now a hole has opened up on its base and it has dumped a billion dollars into a public square — which turned out to not be public, but actually belongs to a few suddenly-very-rich dudes. You can’t blame users for becoming hooting primates when a giant spaceship dumps a billion dollars out of its money hole. It’s like the monolith in the movie 2001 appeared filled with candy and a sign on the front that said “NO CANDY FOR YOU.”
F-22 pilot air supply issue still not resolved
Strategy Page has an update on the F-22 and the ongoing investigation into air supply problems for the pilot:
The U.S. Air Force is admitting that it is having a problem with the pilot air supply on the F-22, a problem they have not been able to find the cause of. Despite this, the air force is going to continue flying its F-22s. The decision to keep flying was made because the air supply problems have not killed anyone yet and they are rare (once every 10,000 sorties.)
The 14 incidents so far were all cases of F-22 pilots apparently experiencing problems. The term “apparently” is appropriate because the pilots did not black out and a thorough check of the air supply system and the aircraft found nothing wrong. There have been nearly 30 of these “dizziness or disorientation” incidents in the last four years, with 14 of them serious enough to be called real incidents. Only one F-22 has been lost to an accident so far and, while that did involve an air supply issue, it was caused by pilot error, not equipment failure.
Meanwhile the air force is spending $7 million to install commercial oxygen status sensors in the air supply systems of its F-22 fighters. This is part of a year-long effort to find out what’s causing the air supply on F-22s to get contaminated and cause pilots to become disoriented or pass out. Twice in the past year the entire F-22 fleet was grounded because of the air supply problems. The first grounding lasted 140 days and ended last September. The second grounding lasted a week and ended five months ago. The 180 F-22s comprise the most powerful component of the air force’s air combat capability and the brass are eager to find out what is wrong.
April 8, 2012
The chronicle of the declining “old media” empires
Matt Welch explains why, even though more reporting is being done now than ever before in human history, the “old media” portrays the situation in the same way the dinosaurs might view the end of their era:
Imagine for a moment that the hurly-burly history of American retail was chronicled not by reporters and academics but by life-long employees of A&P, a largely forgotten supermarket chain that enjoyed a 75 percent market share as recently as the 1950s. How do you suppose an A&P Organization Man might portray the rise of discount super-retailer Wal-Mart, or organic foods-popularizer Whole Foods, let alone such newfangled Internet ventures as Peapod.com? Life looks a hell of a lot different from the perspective of a dinosaur slowly leaking power than it does to a fickle consumer happily gobbling up innovation wherever it shoots up.
That is largely where we find ourselves in the journalism conversation of 2012, with a dreary roll call of depressive statistics invariably from the behemoth’s point of view: newspaper job losses, ad-spending cutbacks, shuttered bureaus, plummeting stock prices, major-media bankruptcies. Never has there been more journalism produced or consumed, never has it been easier to find or create or curate news items, and yet this moment is being portrayed by self-interested insiders as a tale of decline and despair.
It is no insult to the hard work and good faith of either newspaper reporters or media-beat writers (and I’ve been both) to acknowledge that their conflict of interest in this story far exceeds that of, say, academic researchers who occasionally take corporate money, or politicians who pocket campaign donations from entities they help regulate, to name two perennial targets of newspaper editorial boards. We should not expect anything like impartial analysis from people whose very livelihoods—and those of their close friends—are directly threatened by their subject matter.
This goes a long way toward explaining a persistent media-criticism dissonance that has been puzzling observers since at least the mid-1990s: Successful, established journalism insiders tend to be the most dour about the future of the craft, while marginalized and even unpaid aspirants are almost giddy about what might come next. More kids than ever go to journalism school; more commencement speeches than ever warn graduates that, sadly, there’s no more gold in them thar hills. Consumers are having palpable fun finding, sharing, packaging, supplementing, and dreaming up pieces of editorial content; newsroom veterans are consistently among the most depressed of all modern professionals.
April 7, 2012
Arizona’s internet-trolls-go-to-jail bill
Interestingly, aside from the occasional mention of the Arizona Cardinals, almost every post I’ve marked with the Arizona tag over the last three years is about stupid laws or bills that infringe constitutional rights. What up, Arizona?