Techdirt‘s Mike Masnick on the no-we’re-actually-serious “joke” PRSM network:
Soon after the very earliest reporting on Ed Snowden’s leaked documents about PRISM, the folks from Datacoup put together the very amusing GETPRSM website, which looks very much like the announcement of a new social network, but (the joke is) it’s really the NSA scooping up all our data and making the connections. It’s pretty funny. Except, of course, when you find out that it’s real. And, yes, that seems to be the latest revelation out of Ed Snowden’s leaks. The NY Times has an article by James Risen and Laura Poitras (what a combo reporting team there!) detailing how the NSA has basically built its own “shadow” social network in which it tries to create a “social graph” of pretty much everyone that everyone knows, foreign or American, and it all happens (of course) without a warrant. And, note, this is relatively new:
The agency was authorized to conduct “large-scale graph analysis on very large sets of communications metadata without having to check foreignness” of every e-mail address, phone number or other identifier, the document said. Because of concerns about infringing on the privacy of American citizens, the computer analysis of such data had previously been permitted only for foreigners.
The agency can augment the communications data with material from public, commercial and other sources, including bank codes, insurance information, Facebook profiles, passenger manifests, voter registration rolls and GPS location information, as well as property records and unspecified tax data, according to the documents. They do not indicate any restrictions on the use of such “enrichment” data, and several former senior Obama administration officials said the agency drew on it for both Americans and foreigners.
There were apparently two policy changes that allowed this to happen, and both occurred in the past three years. First, in November of 2010, the NSA was allowed to start looking at phone call and email logs of Americans to try to help figure out associations for “foreign intelligence purposes.” Note that phrase. We’ll come back to it. For years, the NSA had been barred from viewing any content on US persons, and the NSA, President Obama and others have continued to insist to this day that there are minimization procedures that prevent spying on Americans. Except, this latest revelation shows that, yet again, this isn’t actually true.

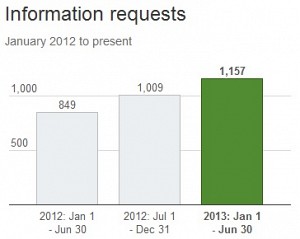 You know you’ve arrived as an online media operation when governments take an interest in who is speaking out, and make efforts to muzzle what’s published. That’s definitely the case with Twitter, the microblogging platform that started as an outlet for exhibitionist ADHD sufferers, only to become a powerful medium for sharing news and grassroots organizing. According to the company’s latest transparency report, governments around the world are issuing ever-more demands for information about the service’s users, and stepping up efforts to suppress tweeted content.
You know you’ve arrived as an online media operation when governments take an interest in who is speaking out, and make efforts to muzzle what’s published. That’s definitely the case with Twitter, the microblogging platform that started as an outlet for exhibitionist ADHD sufferers, only to become a powerful medium for sharing news and grassroots organizing. According to the company’s latest transparency report, governments around the world are issuing ever-more demands for information about the service’s users, and stepping up efforts to suppress tweeted content.

