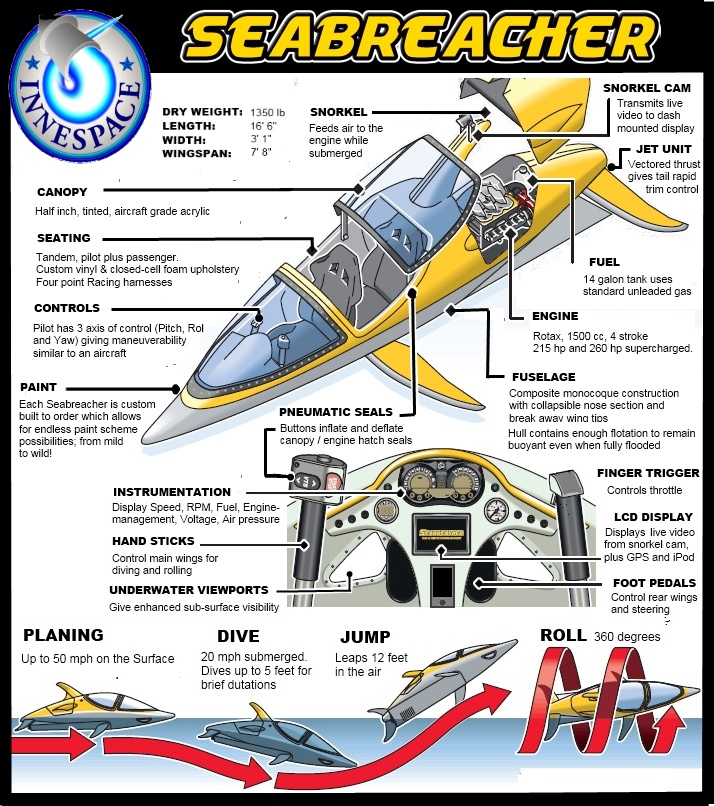
Keeping up with the Joneses has always been a popular hobby among the nouveau riche, and topping the neighbours’ fancy car is only the start of it for some people. If your particular Jones just bought a lovely new pleasure boat, here’s a possible riposte — the Seabreacher J:
The Seabreacher J was designed and engineered exclusively for the recreational boating market. This model incorporates a jet drive for increased safety and better surface performance. The J model is able to be registered as a conventional powerboat. It is powered by a Rotax engine which is available in 155hp or 215hp supercharged variants. The engine and jet drive can be easily maintained at any personal watercraft dealership, making it a very basic watercraft to own and operate. The Seabreacher J combines the thrill of flying a submersible watercraft with the practicality and dependability of a conventional personal watercraft. The J model can be custom built with a host of available options that can personalize your Seabreacher to your desires.
The Seabreacher J isn’t a true submarine, but it’s priced for a larger market. To see what they look like in use, a quick Google Image Search turns up lots of “action shots”. True submersibles are also available for more wealthy customers, as Strategy Page explains:
Since the 1990s there have been a lot of recreational submarines. Luxury boat builders have even built submarine yachts. Submarine construction technology has come a long way in the past century, and it’s possible to build these boats at an affordable ($10-200 million) cost. They are safe and there are over a hundred of them out there.
A few companies have gained a lot of experience building subs for non-military underwater operations (academic research, oil exploration), which has created a body of information and cadre of technicians who can build these recreational subs. One of the largest civilian submarine yards is in Dubai, where dozens have been built so far and construction continues. Another large operation in the U.S. has built most of the scientific subs over the last two decades.
The submersible pleasure craft look like streamlined yachts while on the surface. The upper deck, including the bridge, is outside the pressure hull. When submerging, everyone goes below and the upper deck gets flooded. If you get close to one of these yachts it becomes obvious that they are built to dive. Military subs are still not used to encountering this civilian traffic underwater. The military boats have the right of way, but military boats are now warned to exercise extra care when approaching coastal areas used by civilian subs.
Owners of these luxury subs tend to be secretive, and the builders have agreed to some government oversight, especially to make sure militarized subs, that can carry torpedoes or mines, are not built. But there is no law against anyone owning one of these submarines, and it’s feared that it’s only a matter of time before drug dealers, gun runners, or even terrorists, get their hands on some of them. Some police officials believe this has already happened, but no one is saying much. The civilian subs don’t dive as deep as military subs and are not built for combat. They have staterooms and large windows. But they do have carrying capacity, and that could be put to criminal uses. Already, Colombian gangs have been caught trying to build subs, using Russian advisors initially and later just employing the same tech used for recreational subs. Over a hundred submersibles (a sub that travels just below the surface) have been caught carrying cocaine. The age of privately owned subs is here.