A while back, I mentioned that my hosting service was moving the site to a new server. Fortunately, this change appears to have happened without disrupting anything. Today, however, I had to make a DNS setting change that may take up to 24 hours to take effect. If you get a 404 message that the site is unreachable, try again in an hour or so and hopefully the new settings will be in place. Or, I could be worried over nothing and this will also be a transparent change from the users’ point of view (fingers crossed, anyway).
September 25, 2013
September 24, 2013
Reason.com banned from Reddit‘s /r/Politics subgroup
Nick Gillespie is puzzled that Reddit users are no longer allowed to submit links to Reason:
So I’m left wondering exactly what we did to incur the wrath of TheRedditPope. Reddit penalizes sites and users that scrape articles from original sources, try to game the system by submitting only material in which they have an publishing interest, and don’t add much information or analysis. As several of the commenters in the thread note, Reason.com is the biggest libertarian news site on the web and whether folks agree or not with our take on a given topic, they can’t seriously accuse us of ripping off other sites or not shooting our mouths off with our own particular POVs on any given topics.
Consider the attempted post that brought the ban to our attention. The user who contacted us had apparently tried to submit this story: “Do-Nothing Congress? Americans Think Congress Passes Too Many Laws, Wrong Kinds of Legislation.” Click on the link and you’ll be taken to an extended analysis of information drawn from the latest Reason-Rupe Poll, an original quarterly survey of American voters that has garnered praise from all over the political spectrum and has been cited in all sorts of mainstream and alternative outlets. If the Reason poll — which is designed by Reason Foundation, the nonprofit that publishes this site, and is executed in the field by the same group that conducts Pew Research — and that post in particular don’t meet the threshold of original content that is news-rich and original, then nothing does.
I am a huge admirer of Reddit, even in the wake of recent revelations about the /r/Politics ban. As I wrote last year in a Reddit thread,
Reddit is one of those rare sites that actually delivers on the potential of the Internet and Web to create a new way of creating community and distributing news, information, and culture that simply couldn’t exist in the past. Like wildly different sites ranging from slashdot to Arts & Letters Daily to Talking Points Memo to the late, lamented Suck, Reddit is precisely one of the reasons why cyberspace (or whatever you call it) continues to excite us and make plain old meatspace a little more tolerable.
September 19, 2013
Latest online piracy study shows the problem is Hollywood
Techdirt‘s Mike Masnick shows that the data in the most recent study of online piracy (funded by NBC Universal) clearly shows that the real reason for piracy is Hollywood’s unwillingness or inability to learn:
While we already discussed the MPAA’s questionable new study trying to pin the blame for infringement on Google, MPAA member NBC Universal has released its “Digital Piracy Universe” study as well. This study was done by NetNames, the company formerly known as Envisional, which basically released a very similar study two and a half years ago. Matt Schruers, over at CCIA, does a nice job explaining some of the more questionable aspects of the methodology. However, we’d like to focus on something a bit more basic: the study’s own numbers don’t seem to support what NBC Universal seems to think it does. More specifically, as we noted with the last study, the results actually suggest piracy is Hollywood’s own damn fault. This isn’t just our interpretation either. The guy who wrote both studies, David Price, basically said the same thing right before SOPA died (he argued that the bills were a bad idea).
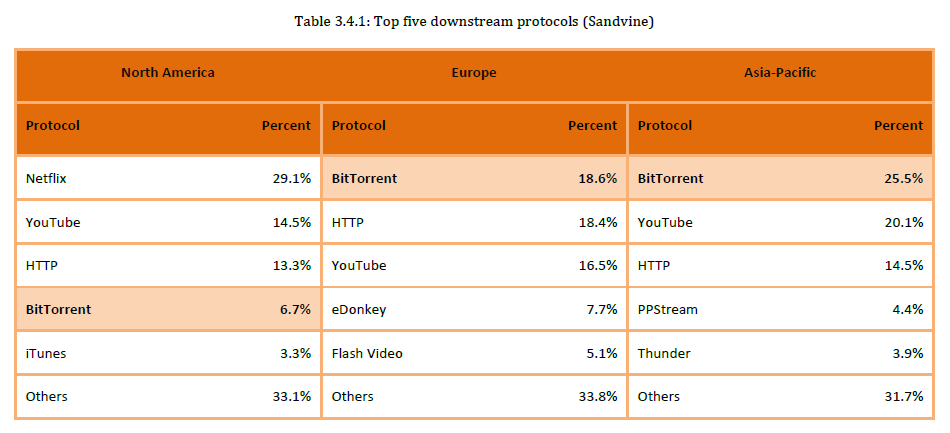
Once again, it’s not difficult to see why the problem is Hollywood’s with one simple chart:
Basically, in the US, where Netflix has come up with a model that many people find to be reasonably priced and convenient enough, the rate of things like BitTorrent usage falls in comparison.
September 18, 2013
The NSA scandal is not about mere privacy
Last week, Yochai Benkler posted this in the Guardian:
The spate of new NSA disclosures substantially raises the stakes of this debate. We now know that the intelligence establishment systematically undermines oversight by lying to both Congress and the courts. We know that the NSA infiltrates internet standard-setting processes to security protocols that make surveillance harder. We know that the NSA uses persuasion, subterfuge, and legal coercion to distort software and hardware product design by commercial companies.
We have learned that in pursuit of its bureaucratic mission to obtain signals intelligence in a pervasively networked world, the NSA has mounted a systematic campaign against the foundations of American power: constitutional checks and balances, technological leadership, and market entrepreneurship. The NSA scandal is no longer about privacy, or a particular violation of constitutional or legislative obligations. The American body politic is suffering a severe case of auto-immune disease: our defense system is attacking other critical systems of our body.
First, the lying. The National Intelligence University, based in Washington, DC, offers a certificate program called the denial and deception advanced studies program. That’s not a farcical sci-fi dystopia; it’s a real program about countering denial and deception by other countries. The repeated misrepresentations suggest that the intelligence establishment has come to see its civilian bosses as adversaries to be managed through denial and deception.
[…]
Second, the subversion. Last week, we learned that the NSA’s strategy to enhance its surveillance capabilities was to weaken internet security in general. The NSA infiltrated the social-professional standard-setting organizations on which the whole internet relies, from National Institute of Standards and Technology to the Internet Engineering Task Force itself, the very institutional foundation of the internet, to weaken the security standards. Moreover, the NSA combined persuasion and legal coercion to compromise the commercial systems and standards that offer the most basic security systems on which the entire internet runs. The NSA undermined the security of the SSL standard critical to online banking and shopping, VPN products central to secure corporate, research, and healthcare provider networks, and basic email utilities.
Serious people with grave expressions will argue that if we do not ruthlessly expand our intelligence capabilities, we will suffer terrorism and defeat. Whatever minor tweaks may be necessary, the argument goes, the core of the operation is absolutely necessary and people will die if we falter. But the question remains: how much of what we have is really necessary and effective, and how much is bureaucratic bloat resulting in the all-too-familiar dynamics of organizational self-aggrandizement and expansionism?
The “serious people” are appealing to our faith that national security is critical, in order to demand that we accept the particular organization of the Intelligence Church. Demand for blind faith adherence is unacceptable.
September 15, 2013
Bruce Schneier on what you can do to stay out of the NSA’s view
Other than going completely off the grid, you don’t have the ability to stay completely hidden, but there are some things you can do to decrease your visibility to the NSA:
With all this in mind, I have five pieces of advice:
- Hide in the network. Implement hidden services. Use Tor to anonymize yourself. Yes, the NSA targets Tor users, but it’s work for them. The less obvious you are, the safer you are.
- Encrypt your communications. Use TLS. Use IPsec. Again, while it’s true that the NSA targets encrypted connections — and it may have explicit exploits against these protocols — you’re much better protected than if you communicate in the clear.
- Assume that while your computer can be compromised, it would take work and risk on the part of the NSA — so it probably isn’t. If you have something really important, use an air gap. Since I started working with the Snowden documents, I bought a new computer that has never been connected to the Internet. If I want to transfer a file, I encrypt the file on the secure computer and walk it over to my Internet computer, using a USB stick. To decrypt something, I reverse the process. This might not be bulletproof, but it’s pretty good.
- Be suspicious of commercial encryption software, especially from large vendors. My guess is that most encryption products from large US companies have NSA-friendly back doors, and many foreign ones probably do as well. It’s prudent to assume that foreign products also have foreign-installed backdoors. Closed-source software is easier for the NSA to backdoor than open-source software. Systems relying on master secrets are vulnerable to the NSA, through either legal or more clandestine means.
- Try to use public-domain encryption that has to be compatible with other implementations. For example, it’s harder for the NSA to backdoor TLS than BitLocker, because any vendor’s TLS has to be compatible with every other vendor’s TLS, while BitLocker only has to be compatible with itself, giving the NSA a lot more freedom to make changes. And because BitLocker is proprietary, it’s far less likely those changes will be discovered. Prefer symmetric cryptography over public-key cryptography. Prefer conventional discrete-log-based systems over elliptic-curve systems; the latter have constants that the NSA influences when they can.
Since I started working with Snowden’s documents, I have been using GPG, Silent Circle, Tails, OTR, TrueCrypt, BleachBit, and a few other things I’m not going to write about. There’s an undocumented encryption feature in my Password Safe program from the command line; I’ve been using that as well.
I understand that most of this is impossible for the typical Internet user. Even I don’t use all these tools for most everything I am working on. And I’m still primarily on Windows, unfortunately. Linux would be safer.
The NSA has turned the fabric of the Internet into a vast surveillance platform, but they are not magical. They’re limited by the same economic realities as the rest of us, and our best defense is to make surveillance of us as expensive as possible.
Trust the math. Encryption is your friend. Use it well, and do your best to ensure that nothing can compromise it. That’s how you can remain secure even in the face of the NSA.
Reining-in the NSA … while it’s still even theoretically possible
In TechDirt, Glyn Moody on the fleeting opportunity to rein-in the NSA:
In the wake of the continuing leaks about the NSA’s activities, most commentators are understandably still trying to get to grips with the enormity of what has been happening. But John Naughton, professor of the public understanding of technology at the UK’s Open University, tackles a very different question on his blog: what is likely to happen in the future, if things carry on as they are?
Naughton notes that the NSA’s mission statement includes the following phrase: “to gain a decision advantage for the Nation and our allies under all circumstances.” “Under all circumstances” means that as the Internet grows — and as we know, it is currently growing rapidly — so the NSA will naturally ask for resources to allow it to do tomorrow what it is doing today: monitoring more or less everything that happens online. Naughton then asks where that might lead if the political climate in the US remains sufficiently favorable to the NSA that it does, indeed, get those resources:
The obvious conclusion therefore, is that unless some constraints on its growth materialise, the NSA will continue to expand. It currently has 35,000 employees. How many will it have in ten years’ time? Who can say: 50,000, maybe? Maybe even more? So we’re confronted with the likelihood of the growth of a bureaucratic monster.
How will such a body be subjected to democratic oversight and control? Let me rephrase that: can such a monster be subjected to democratic control?
September 7, 2013
Maybe the conspiracy theorists just aren’t paranoid enough
Bruce Schneier on the destruction of public trust in government agencies:
I’ve recently seen two articles speculating on the NSA’s capability, and practice, of spying on members of Congress and other elected officials. The evidence is all circumstantial and smacks of conspiracy thinking — and I have no idea whether any of it is true or not — but it’s a good illustration of what happens when trust in a public institution fails.
The NSA has repeatedly lied about the extent of its spying program. James R. Clapper, the director of national intelligence, has lied about it to Congress. Top-secret documents provided by Edward Snowden, and reported on by the Guardian and other newspapers, repeatedly show that the NSA’s surveillance systems are monitoring the communications of American citizens. The DEA has used this information to apprehend drug smugglers, then lied about it in court. The IRS has used this information to find tax cheats, then lied about it. It’s even been used to arrest a copyright violator. It seems that every time there is an allegation against the NSA, no matter how outlandish, it turns out to be true.
Guardian reporter Glenn Greenwald has been playing this well, dribbling the information out one scandal at a time. It’s looking more and more as if the NSA doesn’t know what Snowden took. It’s hard for someone to lie convincingly if he doesn’t know what the opposition actually knows.
All of this denying and lying results in us not trusting anything the NSA says, anything the president says about the NSA, or anything companies say about their involvement with the NSA. We know secrecy corrupts, and we see that corruption. There’s simply no credibility, and — the real problem — no way for us to verify anything these people might say.
September 6, 2013
Bruce Schneier on taking back the internet
From his article in yesterday’s Guardian:
This is not the internet the world needs, or the internet its creators envisioned. We need to take it back.
And by we, I mean the engineering community.
Yes, this is primarily a political problem, a policy matter that requires political intervention.
But this is also an engineering problem, and there are several things engineers can — and should — do.
One, we should expose. If you do not have a security clearance, and if you have not received a National Security Letter, you are not bound by a federal confidentially requirements or a gag order. If you have been contacted by the NSA to subvert a product or protocol, you need to come forward with your story. Your employer obligations don’t cover illegal or unethical activity. If you work with classified data and are truly brave, expose what you know. We need whistleblowers.
We need to know how exactly how the NSA and other agencies are subverting routers, switches, the internet backbone, encryption technologies and cloud systems. I already have five stories from people like you, and I’ve just started collecting. I want 50. There’s safety in numbers, and this form of civil disobedience is the moral thing to do.
Two, we can design. We need to figure out how to re-engineer the internet to prevent this kind of wholesale spying. We need new techniques to prevent communications intermediaries from leaking private information.
We can make surveillance expensive again. In particular, we need open protocols, open implementations, open systems — these will be harder for the NSA to subvert.
The Internet Engineering Task Force, the group that defines the standards that make the internet run, has a meeting planned for early November in Vancouver. This group needs to dedicate its next meeting to this task. This is an emergency, and demands an emergency response.
Update: Glenn Greenwald retweeted this, saying it was “not really hard for a rational person to understand why this is newsworthy”.
Latest NSA news suggests computer security industry has a pretty good racket going. Sell locks to people, then sell the key to gov't.
— Adrian Chen (@AdrianChen) September 5, 2013
Yahoo goes out of its way to lose more long-term users
I moderate a few special interest groups on Yahoo Groups, and I’m subscribed to a couple of dozen others. There’s nothing flashy or exciting about the service: it’s been relatively stable for years, with few changes or disruptions. For most users, this has been ideal. This week Yahoo not only introduced a new logo, they also tossed a stink bomb into the placid Yahoo Groups with a new user interface called “Neo”. They apparently rolled out the changes to a few groups last month, but most users and list owner/moderators hadn’t been given any notice that the change was coming. The Register‘s Kelly Fiveash on the diabolical scheme to annoy long-term users of Yahoo Groups:
‘WTF! MORONS!’ Yahoo! Groups! redesign! traumatises! users!
‘Vile, unfriendly interface’ attacked by world+dog. But format staysYahoo! has told thousands of users who are complaining about the Purple Palace’s pisspoor redesign of its Groups service that it will not be rolled back to the old format — despite a huge outcry.
The Marissa Mayer-run company revamped Yahoo! Groups last week, but it was immediately inundated with unhappy netizens who grumbled that the overhaul was glitchy, difficult to navigate and “severely degraded”.
In response, Yahoo! told its users:
We deeply value how much you, our users, care about Yahoo! Groups … we launched our first update to the Groups experience in several years and while these changes are an important step to building a more modern Groups experience, we recognise that this is a considerable change.
We are listening to all of the community feedback and we are actively measuring user feedback so we can continuously make improvements.
But the complaints have continued to flood in since Yahoo! made the tweak by changing its “classic” (read: ancient) interface to one dubbed “neo” that appeared to have been quickly spewed on to the interwebs with little testing before going live.
And — while the company claimed it was listening closely to its users about the new look Yahoo! Groups — it has ignored pleas from thousands of people who want it to reverse the update.
For users who access Yahoo Groups through the website, the new design has completely befuddled many, hiding functions (and even group names) and making it far more difficult to search for older posts (you reportedly have to search by message number: no other searches are supported). Even for those who only receive email updates, the Neo redesign included odd and sometimes completely unreadable email formatting, broken links, and other highly irritating issues.
This is the real problem with “free” services: when things go wrong, as a user of the service, you don’t have much leverage to complain or to get things fixed.
September 2, 2013
This month in moral panic watch – “rape porn”
British PM David Cameron has decided that it’s the duty of his government to crack down on internet pornography. In particular, the British government will be attempting to stamp out violent pornography, aka “rape porn”. This may not be his best idea ever:
Lobby organisations like “End Violence Against Women” and sensationalist news rags like the Daily Mail repeatedly claim that watching violent pornography increases sexual abuse and rape by men.
However, the scientific evidence has stubbornly refused to play along with this view:
U.S. Commission on Obscenity and Pornography (1970) found no evidence of a causal link between pornography and rape
“Pornography and rape: theory and practice? Evidence from crime data in four countries where pornography is easily available” (1991) B Kutchinsky
Examined what happened to the rape statistics in four countries (USA, Denmark, West Germany and Sweden) during periods where the availability of violent pornography went from extreme scarcity to relative abundance.
Quoting the report: “The results showed that in none of the countries did rape increase more than nonsexual violent crimes. This finding in itself would seem sufficient to discard the hypothesis that pornography causes rape“
There’s also the problem that pornography is actually quite popular — with both male and female users — over 40% of all internet users view pornography voluntarily. In fact, large numbers of women admit to enjoying rape fantasies:
Whether the puritans or the feminists like it or not, it is a fact that many women enjoy rape fantasies as explained by this female journalist.
Erotic literature such as Fifty Shades of Grey featuring bondage, spanking, hair pulling, fisting and pinwheeling generated sales of over £10M in six months, to a predominantly female audience.
On a more scientific level, a 1988 study by Pelletier and Herold found that over half of their female respondents had fantasies of forced sex.
Nobody (quite rightly) suggests that women who expose themselves to this sort of “violent porn” literature, or who engage in sexual fantasies of rape are more likely to go out and put themselves into situations where they will be raped.
People clearly understand that there is a world of difference between enjoying rape as a sexual fantasy and the violent, painful reality of actual rape.
The same reasoning must logically apply to men who enjoy rape fantasy and rape porn. There is a world of difference between enjoying rape as a sexual fantasy and the violent reality of actual raping another human being.
To assert that women can enjoy rape fantasy, porn and violent BDSM literature without harm because they understand the difference between fantasy and reality, but men do not is nothing more than misandry.
September 1, 2013
India moves government email away from US-based email services
Vinay Mandalia discusses the quite rational response of the Indian government to the recent discovery that the US intelligence services have had full access to all email communications hosted on US email services:
The Government of India is planning to ban the use of US based email services like Gmail for official communications and is soon going to send out a formal notification to its half a million officials across the country asking them to use official email addresses and services provided by National Informatics Centre.
The move is intended to increase the security of confidential government data and information after it was revealed earlier that NSA may be involved in widespread spying and surveillance activities across the globe.
In a statement to reporters here J. Satyanarayana, secretary in the department of electronics and information technology, said that data of Indian citizens using US based email services like Gmail is residing on servers which are located outside India and for now the government is concerned about the large amount of official and critical data that may be resident on those servers.
Expect a lot of other US “allies” to suddenly discover that their internal communications have been an open book to their “friends” for the last 10-20 years and decide to take similar measures.
H/T to Techdirt for the link.
August 22, 2013
QotD: Politicians and the world of real jobs
Whenever I hear a politician or pundit talk about a modern economy like they understand it well enough to run it, I want to burst out laughing, or cry, or both. If you can’t even keep pictures of your dick off the Intertunnel during an election cycle, I imagine being Emperor of the Economic and Social Universe is probably well above your abilities. Politicians have to take tours of factories because to them, everything and everybody in a factory might as well be alchemy performed by men from Jupiter.
“Sippican Cottage”, “Mene, Mene, Tekel, Upharsin” Sippican Cottage, 2013-08-21.
August 18, 2013
Rounding up the “government is spying on everyone” news
A linkapalooza of information at Zero Hedge:
- Just weeks after NSA boss Alexander said that a review of NSA spying found not even one violation, the Washington Post published an internal NSA audit showing that the agency has broken its own rules thousands of times each year
- 2 Senators on the intelligence committee said the violations revealed in the Post article were just the “tip of the iceberg”
- Glenn Greenwald notes: “One key to the WashPost story: the reports are internal, NSA audits, which means high likelihood of both under-counting & white-washing”.(Even so, the White House tried to do damage control by retroactively changing on-the-record quotes)
- The government is spying on essentially everything we do. It is not just “metadata” … although that is enough to destroy your privacy
- The government has adopted a secret interpretation of the Patriot Act which allows it to pretend that “everything” is relevant … so it spies on everyone
- NSA whistleblowers say that the NSA collects all of our conversations word-for-word
- It’s not just the NSA … Many other agencies, like the FBI and IRS – concerned only with domestic issues – spy on Americans as well
That’s just the first few items of a long list. Read the whole thing.
August 14, 2013
The “Indie Web” is the very definition of a fringe project
Wired‘s Klint Finley wants you to meet the indie hackers who want to jailbreak the internet (among other things):
One guy is wearing his Google Glass. Another showed up in an HTML5 t-shirt. And then there’s the dude who looks like the Mad Hatter, decked out in a top hat with an enormous white flower tucked into the brim.
At first, they look like any other gaggle of tech geeks. But then you notice that one of them is Ward Cunningham, the man who invented the wiki, the tech that underpins Wikipedia. And there’s Kevin Marks, the former vice president of web services at British Telecom. Oh, and don’t miss Brad Fitzpatrick, creator of the seminal blogging site LiveJournal and, more recently, a coder who works in the engine room of Google’s online empire.
Packed into a small conference room, this rag-tag band of software developers has an outsized digital pedigree, and they have a mission to match. They hope to jailbreak the internet.
They call it the Indie Web movement, an effort to create a web that’s not so dependent on tech giants like Facebook, Twitter, and, yes, Google — a web that belongs not to one individual or one company, but to everyone. “I don’t trust myself,” says Fitzpatrick. “And I don’t trust companies.” The movement grew out of an egalitarian online project launched by Fitzpatrick, before he made the move to Google. And over the past few years, it has roped in about 100 other coders from around the world.
August 13, 2013
Master Sergeant Anonymous
Justine Sharrock talks to someone who claims that there are many members of Anonymous in the ranks of the US military:
Are there a lot of members of Anonymous in the Army?
There are more than you would think, more heavily in the techie world [of the military] — especially at Fort Huachuca, where all the intel people are. A lot of them wanted to get the job [there] because they want to learn secret stuff and have a better personal understanding of how the world actually works.How do you know who is in Anonymous?
Initially we have the handshaking phase. The lingo is still relatively unknown. In conversation, you drop in jokes. If you are with someone on a mission, you’re like, “Man, there are over 9,000 reasons that this is a bad idea.” That initially establishes friendship. Once you feel comfortable with the person and they aren’t just posing as part of the culture, then you talk about what they’ve done and how much a part of it they are. It gets to the point where you are discussing individual operations.What are the most popular operations amongst soldiers?
Anonymous is so distributed and leaderless that everyone has operations they love and hate. Operation Cartel, especially at Fort Bliss. Operation Dark Net was universally loved. And Operation Payback was pretty well received.[…]
Does the military know about the Anonymous presence?
Pre-Manning, there were several academic papers put out trying to analyze it and school the leadership. Because the Army is a very top-down organization, they assume that [Anonymous] is too. Leadership wasn’t concerned with it until Manning happened. Then they read everything under the [lens] of what Manning did and it just scared them — scared them blind. They know we are in there and they assume that we are all going to do a Manning or a Snowden.How have they addressed it?
Every six months you are mandated to get a Threat Awareness and Reporting Procedures Brief. It used to be very much like how to … spot the Iraqi contractor who is pacing off your base. Now it is, “Look at the person at your left and right. Are they espousing social beliefs that don’t line up with Army values? What websites do they go to at work?” With the caveat that it is OK to have political beliefs that are different. You get a heavy-handed feeling.I have had more than a few officers come up to me and as we are trying to talk about [Anonymous] they are worried, like, “Are you CID [working undercover for the Central Investigative Division]?” Because you always worry about that.