Published on 22 May 2014
One of the most talked about technology tradeoffs today is the question of how much privacy we give up to live in a world of convenience, speed and intelligence. We’re now less anonymous than many people are aware of or comfortable with, and headline-grabbing stories like the Heartbleed Bug don’t provide much reassurance for those of us seeking comfort around data privacy. How can we balance our need for anonymity with the incredible benefits of our connected world? World class Internet privacy expert Dr. Michael Geist helps us understand which current surveillance and privacy issues should be on your mind.
Dr. Michael Geist is a law professor at the University of Ottawa where he holds the Canada Research Chair in Internet and E-commerce Law. He has obtained a Bachelor of Laws (LL.B.) degree from Osgoode Hall Law School in Toronto, Master of Laws (LL.M.) degrees from Cambridge University in the UK and Columbia Law School in New York, and a Doctorate in Law (J.S.D.) from Columbia Law School. Dr. Geist is an internationally syndicated columnist on technology law issues with his regular column appearing in the Toronto Star and the Ottawa Citizen. Dr. Geist is the editor of From “Radical Extremism” to “Balanced Copyright”: Canadian Copyright and the Digital Agenda (2010) and In the Public Interest: The Future of Canadian Copyright Law (2005), both published by Irwin Law, the editor of several monthly technology law publications, and the author of a popular blog on Internet and intellectual property law issues.
Dr. Geist serves on many boards, including the CANARIE Board of Directors, the Canadian Legal Information Institute Board of Directors, the Privacy Commissioner of Canada’s Expert Advisory Board, the Electronic Frontier Foundation Advisory Board, and on the Information Program Sub-Board of the Open Society Institute. He has received numerous awards for his work including the Kroeger Award for Policy Leadership and the Public Knowledge IP3 Award in 2010, the Les Fowlie Award for Intellectual Freedom from the Ontario Library Association in 2009, the Electronic Frontier Foundation’s Pioneer Award in 2008, Canarie’s IWAY Public Leadership Award for his contribution to the development of the Internet in Canada and he was named one of Canada’s Top 40 Under 40 in 2003. In 2010, Managing Intellectual Property named him on the 50 most influential people on intellectual property in the world.
May 24, 2014
Michael Geist – Who’s Watching Whom?
The technological democratization of law enforcement and the rise of “Little Brother”
If you care about your privacy, you’re equally worried about the intrusive surveillance state and the unconstrained snooping of corporations. You may now need to worry about your snoopy neighbours also getting in on the act, as Declan McCullagh explains on Google+. This is a response to someone on a private mailing list for Silicon Valley folks, who said that he had no issue with automated collection of license plate data:
Tomorrow one of your PV [Portola Valley] neighbors will set up a computer-connected camera on private property and aimed at the street. It records all those “plates exposed” going by and, by doing optical character recognition with free software such as ANPR MX (C# code, BSD-licensed), it records every time a car goes by. The DMV will happily provide drivers’ names based on the license plate*; there’s even a process for “bulk quantities” of data.** That information doesn’t include a home address, but that’s easy to come by through other searches.
Then the neighbor launches PVPeopleTracker.com. It updates in real time showing whenever someone is at home, and marks their house in bright red if they’re gone on an extended trip. If there are odd patterns of movement compared to a baseline — perhaps suspicious late-night outings — those can be flagged as well. Any visitor to PVPeopleTracker.com can sign up for handy free email alerts reporting at what time their targeted house becomes vacant each weekday morning. Other network-linked cameras in PV can supplement the PVPeopleTracker.com database, so that everyone driving in town will have their movements monitored, archived, and publicly visible at all times.
With more than one network-linked camera separated by a known distance by roads with known speed limits, it would be simple to calculate speeding violations and send automated alerts, with MP4 videos attached as evidence, to the sheriff and CHP. PVPeopleTracker.com can also be cross-referenced against databases showing, say, marijuana convictions; if your movement profile matches a known drug trafficker, law enforcement can be alerted. (Sorry about those false positives!)
May 23, 2014
“Mammals don’t respond well to surveillance. We consider it a threat. It makes us paranoid, and aggressive and vengeful”
Angelique Carson reports on a recent IAPP Canada Privacy Symposium presentation:
If marine biologist-turned-best-selling author Peter Watts is an expert on anything, it’s mammals. Speaking to 400 or so privacy pros and regulators gathered last week at the IAPP Canada Privacy Symposium to talk privacy and data protection, he used that experience to send a rather jarring — and anything but conventional — message:
Mammals don’t respond well to surveillance. We consider it a threat. It makes us paranoid, and aggressive and vengeful. But we’ll never win against the giant corporations and governments that watch us, Watts argued, so all we can develop is a surefire defense.
Think “scorched earth.” If we can’t protect the data, Watts posited, maybe we should burn it to the ground.
Hear him out: Mammals will always respond to the surveillance threat as they would any threat — with aggression, in the same way the natural selection process has shaped every other life form on this planet.
“Anybody who thinks their own behavior isn’t at least partly informed by those legacy circuits has not been paying attention,” he said.
Watts pointed to author David Brin’s assertion during his keynote recently at the IAPP’s Global Privacy Summit that while our instinct is to pass a law aimed at telling governments and corporations to “stop looking” at us, we should instead turn our gaze to them in the name of reciprocity.
“It’s not telling them do not look,” Brin said during his speech. “It’s looking back.”
But Edward Snowden is currently living in Russia after he tried to “look back.” And as someone who’s worked a lot in the past with mammals, Watts knows that, biologically, looking back is a bad idea: “To get into a staring contest with a large, aggressive, territorial mammal primed to think of eye contact as a threat display … I can’t recommend it.”
“Natural selection favors the paranoid,” Watts said.
H/T to Bruce Schneier for the link.
May 19, 2014
“Parallel construction” and Godwinizing the NSA
At Popehat, Clark uses an excerpt from a Bruce Schneier post to make a larger point. Here’s what Bruce wrote last year:
This dynamic was vitally important during World War II. During the war, the British were able to break the German Enigma encryption machine and eavesdrop on German military communications. But while the Allies knew a lot, they would only act on information they learned when there was another plausible way they could have learned it. They even occasionally manufactured plausible explanations. It was just too risky to tip the Germans off that their encryption machines’ code had been broken.
And this is Clark’s take:
We know that the NSA collects all sorts of information on American citizens. We know that the FBI and the CIA have full access to this information. We know that the DEA also has full access to that data. And we know that when the DEA busts someone using information gleaned by the electronic panopticon of our internal spy organization, they take pains to hide the source of the information via the subterfuge of parallel construction.
The insight is this: our government is now dealing with the citizenry the same way that the British dealt with the Nazis: treating them as an external existential threat, spying on them, and taking pains to obfuscate the source of the information that they use to target their attacks.
Yeah, Godwin’s law, whatever, whatever. My point is NOT that the NSA is the same as the Nazi party (in fact, my argument has the NSA on the opposite side). My point is that the government now treats ordinary civilians as worthy of the same sort of tactics that they once used against the Nazis.
H/T to Bernard King for the link.
May 15, 2014
The NSA’s self-described mission – “Collect it all. Know it all. Exploit it all.”
In The Atlantic, Conor Friedersdorf reviews Glenn Greenwald’s new book, No Place to Hide:
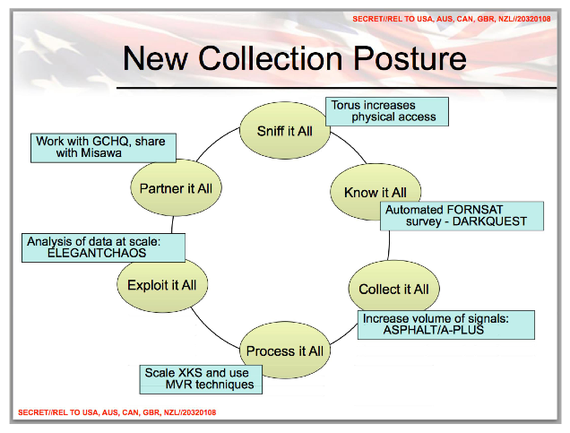
Collect it all. Know it all. Exploit it all.
That totalitarian approach came straight from the top. Outgoing NSA chief Keith Alexander began using “collect it all” in Iraq at the height of the counterinsurgency. Eventually, he aimed similar tools at hundreds of millions of innocent people living in liberal democracies at peace, not war zones under occupation.
The strongest passages in No Place to Hide convey the awesome spying powers amassed by the U.S. government and its surveillance partners; the clear and present danger they pose to privacy; and the ideology of the national-security state. The NSA really is intent on subverting every method a human could use to communicate without the state being able to monitor the conversation.
U.S. officials regard the unprecedented concentration of power that would entail to be less dangerous than the alternative. They can’t conceive of serious abuses perpetrated by the federal government, though recent U.S. history offers many examples.
[…]
But it is a mistake (albeit a common one) to survey the NSA-surveillance controversy and to conclude that Greenwald represents the radical position. His writing can be acerbic, mordant, biting, trenchant, scathing, scornful, and caustic. He is stubbornly uncompromising in his principles, as dramatized by how close he came to quitting The Guardian when it wasn’t moving as fast as he wanted to publish the first story sourced to Edward Snowden. Unlike many famous journalists, he is not deferential to U.S. leaders.
Yet tone and zeal should never be mistaken for radicalism on the core question before us: What should America’s approach to state surveillance be? “Defenders of suspicionless mass surveillance often insist … that some spying is always necessary. But this is a straw man … nobody disagrees with that,” Greenwald explains. “The alternative to mass surveillance is not the complete elimination of surveillance. It is, instead, targeted surveillance, aimed only at those for whom there is substantial evidence to believe they are engaged in real wrongdoing.”
That’s as traditionally American as the Fourth Amendment.
Targeted surveillance “is consistent with American constitutional values and basic precepts of Western justice,” Greenwald continues. Notice that the authority he most often cites to justify his position is the Constitution. That’s not the mark of a radical. In fact, so many aspects of Greenwald’s book and the positions that he takes on surveillance are deeply, unmistakably conservative.
May 11, 2014
The NSA worked very hard to set themselves up for the Snowden leaks
A few days back, Charles Stross pointed out one of the most ironic points of interest in the NSA scandal … they did it to themselves, over the course of several years effort:
I don’t need to tell you about the global surveillance disclosures of 2013 to the present — it’s no exaggeration to call them the biggest secret intelligence leak in history, a monumental gaffe (from the perspective of the espionage-industrial complex) and a security officer’s worst nightmare.
But it occurs to me that it’s worth pointing out that the NSA set themselves up for it by preventing the early internet specifications from including transport layer encryption.
At every step in the development of the public internet the NSA systematically lobbied for weaker security, to enhance their own information-gathering capabilities. The trouble is, the success of the internet protocols created a networking monoculture that the NSA themselves came to rely on for their internal infrastructure. The same security holes that the NSA relied on to gain access to your (or Osama bin Laden’s) email allowed gangsters to steal passwords and login credentials and credit card numbers. And ultimately these same baked-in security holes allowed Edward Snowden — who, let us remember, is merely one guy: a talented system administrator and programmer, but no Clark Kent — to rampage through their internal information systems.
The moral of the story is clear: be very cautious about poisoning the banquet you serve your guests, lest you end up accidentally ingesting it yourself.
May 6, 2014
Reset the Net on June 5th
At Wired, Kim Zetter talks about an initiative to reclaim (some measure of) privacy on the internet:
A coalition of nearly two-dozen tech companies and civil liberties groups is launching a new fight against mass internet surveillance, hoping to battle the NSA in much the same way online campaigners pushed back on bad piracy legislation in 2012.
The new coalition, organized by Fight for the Future, is planning a Reset the Net day of action on June 5, the anniversary of the date the first Edward Snowden story broke detailing the government’s PRISM program, based on documents leaked by the former NSA contractor.
“Government spies have a weakness: they can hack anybody, but they can’t hack everybody,” the organizers behind the Reset the Net movement say in their video (above). “Folks like the NSA depend on collecting insecure data from tapped fiber. They depend on our mistakes, mistakes we can fix.”
To that end, the groups are calling on developers to add at least one NSA resistant feature to mobile apps, and on websites to add security features like SSL (Secure Socket Layer), HSTS (HTTP Strict Transport Security), and Perfect Forward Secrecy to better secure the communication of users and thwart government man-in-the-middle attacks.
April 13, 2014
Ephemeral apps and the NSA
Bruce Schneier on the rising popularity of apps that only leave your content visible briefly and then automatically removes it:
Ephemeral messaging apps such as Snapchat, Wickr and Frankly, all of which advertise that your photo, message or update will only be accessible for a short period, are on the rise. Snapchat and Frankly, for example, claim they permanently delete messages, photos and videos after 10 seconds. After that, there’s no record.
This notion is especially popular with young people, and these apps are an antidote to sites such as Facebook where everything you post lasts forever unless you take it down—and taking it down is no guarantee that it isn’t still available.
These ephemeral apps are the first concerted push against the permanence of Internet conversation. We started losing ephemeral conversation when computers began to mediate our communications. Computers naturally produce conversation records, and that data was often saved and archived.
[…]
At best, the data is recorded, used, saved and then deliberately deleted. At worst, the ephemeral nature is faked. While the apps make the posts, texts or messages unavailable to users quickly, they probably don’t erase them off their systems immediately. They certainly don’t erase them from their backup tapes, if they end up there.
The companies offering these apps might very well analyze their content and make that information available to advertisers. We don’t know how much metadata is saved. In SnapChat, users can see the metadata even though they can’t see the content and what it’s used for. And if the government demanded copies of those conversations — either through a secret NSA demand or a more normal legal process involving an employer or school — the companies would have no choice but to hand them over.
Even worse, if the FBI or NSA demanded that American companies secretly store those conversations and not tell their users, breaking their promise of deletion, the companies would have no choice but to comply.
That last bit isn’t just paranoia.
April 7, 2014
April 2, 2014
People are less inclined to shop or bank online after NSA surveillance reports
Among the side-effects of government surveillance revelations, ordinary people are deciding to be a bit less involved in online activities, according to a new Harris Poll:
Online banking and shopping in America are being negatively impacted by ongoing revelations about the National Security Agency’s digital surveillance activities. That is the clear implication of a recent ESET-commissioned Harris poll which asked more than 2,000 U.S. adults ages 18 and older whether or not, given the news about the NSA’s activities, they have changed their approach to online activity.
Almost half of respondents (47%) said that they have changed their online behavior and think more carefully about where they go, what they say, and what they do online.
When it comes to specific Internet activities, such as email or online banking, this change in behavior translates into a worrying trend for the online economy: over one quarter of respondents (26%) said that, based on what they have learned about secret government surveillance, they are now doing less banking online and less online shopping. This shift in behavior is not good news for companies that rely on sustained or increased use of the Internet for their business model.
[…]
Whether or not we have seen the full extent of the public’s reaction to state-sponsored mass surveillance is hard to predict, but based on this survey and the one we did last year, I would say that, if the NSA revelations continue – and I am sure they will – and if government reassurances fail to impress the public, then it is possible that the trends in behavior we are seeing right now will continue. For example, I do not see many people finding reassurance in President Obama’s recently announced plan to transfer the storage of millions of telephone records from the government to private phone companies. As we will document in our next installment of survey findings, data gathering by companies is even more of a privacy concern for some Americans than government surveillance.
And in case anyone is tempted to think that this is a narrow issue of concern only to news junkies and security geeks, let me be clear: according to this latest survey, 85% of adult Americans are now at least somewhat familiar with the news about secret government surveillance of private citizens’ phone calls, emails, online activity, and so on.
March 13, 2014
It’s amazing how much data can be derived from “mere” metadata
Two Stanford grad students conducted a research project to find out what kind of actual data can be derived from mobile phone metadata:
Two Stanford computer science students were able to acquire detailed information about people’s lives just from telephone metadata — the phone number of the caller and recipient, the particular serial number of the phones involved, the time and duration of calls and possibly the location of each person when the call occurred.
The researchers did not do any illegal snooping — they worked with the phone records of 546 volunteers, matching phone numbers against the public Yelp and Google Places directories to see who was being called.
From the phone numbers, it was possible to determine that 57 percent of the volunteers made at least one medical call. Forty percent made a call related to financial services.
The volunteers called 33,688 unique numbers; 6,107 of those numbers, or 18 percent, were isolated to a particular identity.
[…]
They crowdsourced the data using an Android application and conducted an analysis of individual calls made by the volunteers to sensitive numbers, connecting the patterns of calls to emphasize the detail available in telephone metadata, Mayer said.
“A pattern of calls will, of course, reveal more than individual call records,” he said. “In our analysis, we identified a number of patterns that were highly indicative of sensitive activities or traits.”
For example, one participant called several local neurology groups, a specialty pharmacy, a rare-condition management service, and a pharmaceutical hotline used for multiple sclerosis.
Another contacted a home improvement store, locksmiths, a hydroponics dealer and a head shop.
The researchers initially shared the same hypothesis as their computer science colleagues, Mayer said. They did not anticipate finding much evidence one way or the other.
“We were wrong. Phone metadata is unambiguously sensitive, even over a small sample and short time window. We were able to infer medical conditions, firearm ownership and more, using solely phone metadata,” he said.
February 11, 2014
QotD: The NSA voicemail greeting
Thanks for calling the National Security Agency. Press 1 for a blanket denial. Whatever you heard, it’s not true. Press 2 to hear a transcript of every call you’ve ever made. Press 3 to confess. If you haven’t done anything, that’s OK, the NSA treats everyone like a criminal. Press 4 to have your tax money used to violate your privacy. Press 5 to hear these options again.
Gregg Easterbrook, “Are the Chiefs real or opportunistic?”, ESPN Tuesday Morning Quarterback, 2013-10-29
January 26, 2014
The New York Times profiles Rand Paul
An interesting view of Rand Paul by Sam Tanenhaus and Jim Rutenberg:
As Rand Paul test-markets a presidential candidacy and tries to broaden his appeal, he is also trying to take libertarianism, an ideology long on the fringes of American politics, into the mainstream. Midway through his freshman term, he has become a prominent voice in Washington’s biggest debates — on government surveillance, spending and Middle East policy.
In the months since he commanded national attention and bipartisan praise for his 13-hour filibuster against the Obama administration’s drone strike program, Mr. Paul has impressed Republican leaders with his staying power, in part because of the stumbles of potential rivals and despite some of his own.
“Senator Paul is a credible national candidate,” said Mitt Romney, who ran for president as the consummate insider in 2012. “He has tapped into the growing sentiment that government has become too large and too intrusive.” In an email, Mr. Romney added that the votes and dollars Mr. Paul would attract from his father’s supporters could help make him “a serious contender for the Republican nomination.”
But if Mr. Paul reaps the benefits of his father’s name and history, he also must contend with the burdens of that patrimony. And as he has become a politician in his own right and now tours the circuit of early primary states, Mr. Paul has been calibrating how fully he embraces some libertarian precepts.
[…]
Since becoming a national figure, Mr. Paul has generally stayed on safer ground. His denunciations of government intrusion on Americans’ privacy have been joined by lawmakers in both parties and have resonated with the public — though no other member of Congress as yet has joined him in his planned class-action suit against the National Security Agency.
He has renounced many of the isolationist tenets central to libertarianism, backed away from his longstanding objections to parts of the 1964 Civil Rights Act and teamed with members of the Congressional Black Caucus in calling for an easing of drug-sentencing laws. He recently unveiled a plan for investment in distressed inner cities.
Much of that is in keeping with the left-right alliance Mr. Paul promotes, an alternative to what he dismisses as a “mushy middle.” Such partnerships, he says, “include people who firmly do believe in the same things, that happen to serve in different parties.”
Of course, no profile of Rand Paul is complete without including his early influences, including his musical tastes:
Rand was engrossed in his own course of libertarian study: He received a set of Ayn Rand novels for his 17th birthday. And he followed the rock band Rush, some of whose lyrics had libertarian themes.
Gary L. Gardner Jr., a high school friend, said: “I remember even back then being on a swim team bus and a Rush song comes on. I think it was the song ‘Trees’ — and he said, ‘Man, listen to the words of this, you know those guys have got to be conservative.’ ”
“The Trees” tells the story of maples, overshadowed by tall oaks, that form a union to bring equality to the woods “by hatchet, ax and saw.”
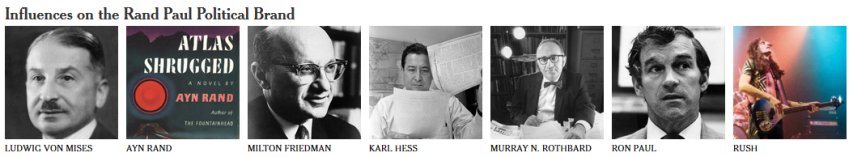
The pantheon of libertarianism includes economists like Mises and Friedman and the novelist Rand; Mr. Hess, a former speechwriter for Senator Barry M. Goldwater; Mr. Rothbard, an economic historian and social thinker; Ron Paul, congressman, presidential aspirant, father and “hero”; and Rush, whose lyrics were infused with libertarian themes.