One of the interesting things about being a participant-observer anthropologist, as I am, is that you often develop implicit knowledge that doesn’t become explicit until someone challenges you on it. The seed of this post was on a recent comment thread where I was challenged to specify the difference between a geek and a hacker. And I found that I knew the answer. Geeks are consumers of culture; hackers are producers.
Thus, one doesn’t expect a “gaming geek” or a “computer geek” or a “physics geek” to actually produce games or software or original physics — but a “computer hacker” is expected to produce software, or (less commonly) hardware customizations or homebrewing. I cannot attest to the use of the terms “gaming hacker” or “physics hacker”, but I am as certain as of what I had for breakfast that computer hackers would expect a person so labeled to originate games or physics rather than merely being a connoisseur of such things.
[. . .]
All hackers are, almost by definition, geeks — but the reverse is not true.
Eric S. Raymond, “Geeks, hackers, nerds, and crackers: on language boundaries”, Armed and Dangerous, 2011-01-09
January 10, 2011
QotD: Geeks and Hackers defined
December 16, 2010
Bruce Schneier on Security in 2020
Aside from all the ugly new terms coined to describe the phenomena, the evolution of security is one of the most under-appreciated stories of the decade. The next decade is going to be even more important to how we live our lives:
There’s really no such thing as security in the abstract. Security can only be defined in relation to something else. You’re secure from something or against something. In the next 10 years, the traditional definition of IT security — that it protects you from hackers, criminals, and other bad guys — will undergo a radical shift. Instead of protecting you from the bad guys, it will increasingly protect businesses and their business models from you.
Ten years ago, the big conceptual change in IT security was deperimeterization. A wordlike grouping of 18 letters with both a prefix and a suffix, it has to be the ugliest word our industry invented. The concept, though — the dissolution of the strict boundaries between the internal and external network — was both real and important.
So, that was then. This is now:
Today, two other conceptual changes matter. The first is consumerization. Another ponderous invented word, it’s the idea that consumers get the cool new gadgets first, and demand to do their work on them. Employees already have their laptops configured just the way they like them, and they don’t want another one just for getting through the corporate VPN. They’re already reading their mail on their BlackBerrys or iPads. They already have a home computer, and it’s cooler than the standard issue IT department machine. Network administrators are increasingly losing control over clients.
This trend will only increase. Consumer devices will become trendier, cheaper, and more integrated; and younger people are already used to using their own stuff on their school networks. It’s a recapitulation of the PC revolution. The centralized computer center concept was shaken by people buying PCs to run VisiCalc; now it’s iPads and Android smart phones.
I’ve certainly noticed this myself: it was forced to my attention a couple of years ago, when a change of employment required me to buy and maintain my own “business” computer and software. Without seriously stressing my wallet, I was able to buy far more capable equipment than my previous employer had provided. Being able to check my email on multiple devices was very important, and once I’d started doing that, I realized the need to do many other things regardless of the machine I happened to be using. There are, of course, trade-offs involved:
The second conceptual change comes from cloud computing: our increasing tendency to store our data elsewhere. Call it decentralization: our email, photos, books, music, and documents are stored somewhere, and accessible to us through our consumer devices. The younger you are, the more you expect to get your digital stuff on the closest screen available. This is an important trend, because it signals the end of the hardware and operating system battles we’ve all lived with. Windows vs. Mac doesn’t matter when all you need is a web browser. Computers become temporary; user backup becomes irrelevant. It’s all out there somewhere — and users are increasingly losing control over their data.
Anyway, there’s lots more interesting stuff. Go read the whole thing.
December 14, 2010
No surprises at all in Gawker’s 50 most-popular passwords
An article in the Wall Street Journal has the 50 most popular passwords from the Gawker data heist:
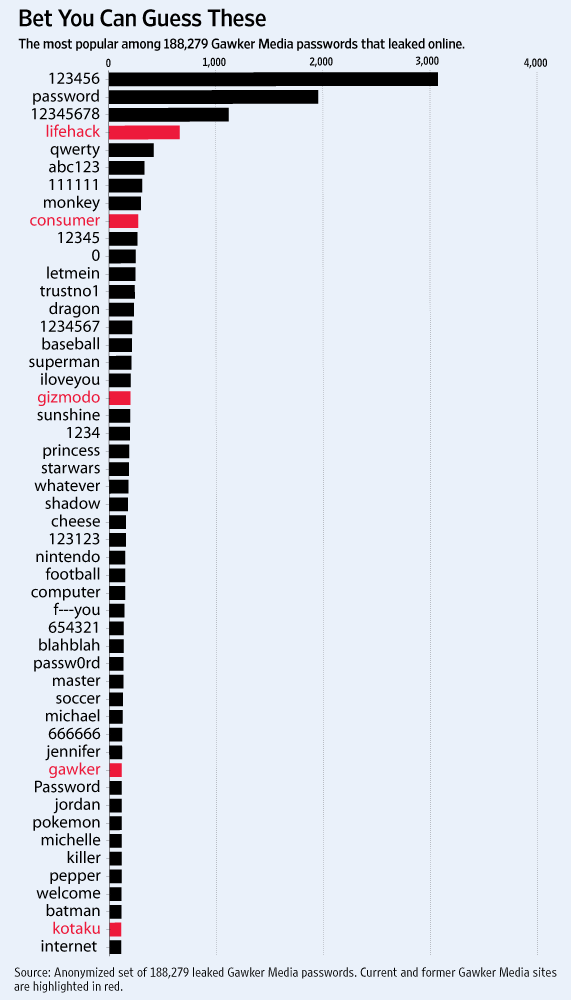
Recognize the pattern? Here’s a word cloud from my last post on passwords:
Other posts on this topic: Passwords and the average user, More on passwords, And yet more on passwords, and Practically speaking, the end is in sight for passwords.
November 18, 2010
QotD: On the quality of writing, mediated through technology
I own a computer. I don’t use the Internet very much. I’m not a technophobe. It just doesn’t help me very much. Writing is a slow and a difficult process mentally. How you physically render the words onto a screen or a page doesn’t help you. I’ll give you this example. When words had to be carved into stone, with a chisel, you got the Ten Commandments. When the quill pen had been invented and you had to chase a goose around the yard and sharpen the pen and boil some ink and so on, you got Shakespeare. When the fountain pen came along, you got Henry James. When the typewriter came along, you got Jack Kerouac. And now that we have the computer, we have Facebook. Are you seeing a trend here?
P.J. O’Rourke, “Very Little That Gets Blogged Is Of Very Much Worth”, Radio Free Europe/Radio Liberty, 2010-11-18
October 21, 2010
October 14, 2010
Little Bobby Tables must speak Swedish
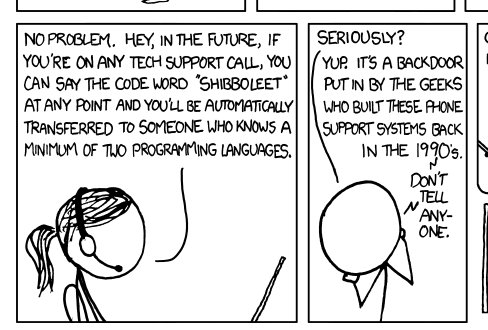
By way of Bruce Schneier an opportunity to show another xkcd comic:
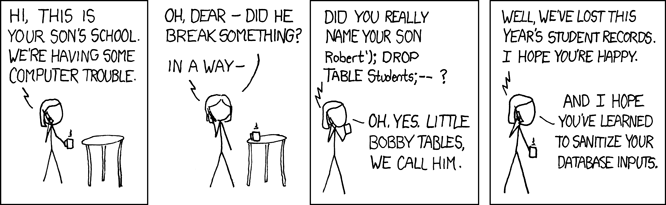
So, what’s the Swedish tie-in?
As you may have heard, we’ve had a very close election here in Sweden. Today the Swedish Election Authority published the hand written votes. While scanning through them I happened to notice
R;13;Hallands län;80;Halmstad;01;Halmstads västra valkrets;0904;Söndrum 4;pwn DROP TABLE VALJ;1
The second to last field is the actual text on the ballot. Could it be that Little Bobby Tables is all grown up and has migrated to Sweden? Well, it’s probably just a joke but even so it brings questions since an SQL-injection on election data would be very serious.
September 15, 2010
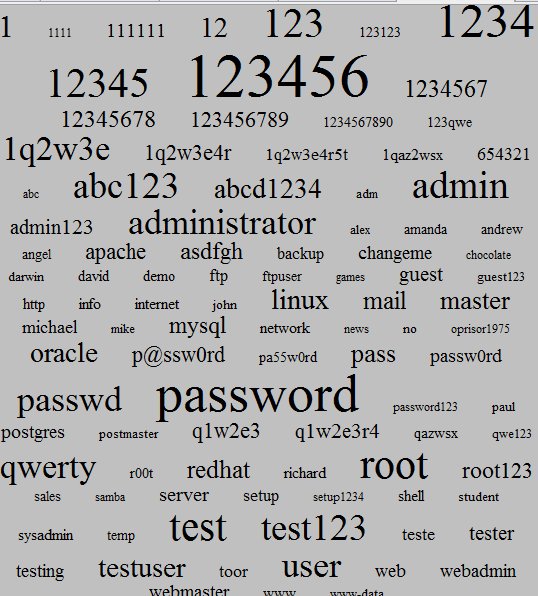
Recognize your password?
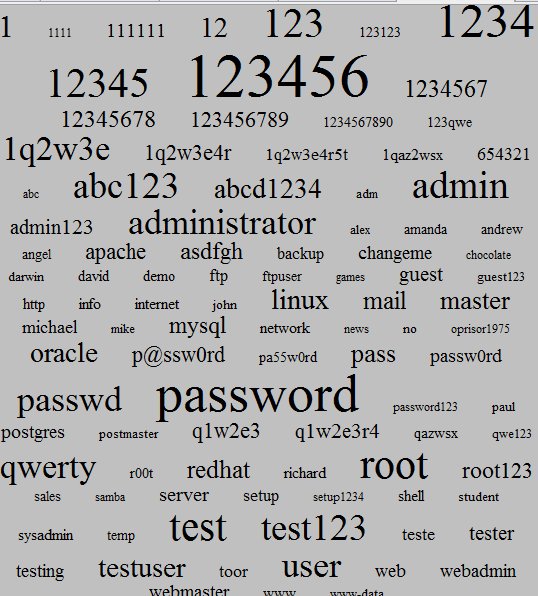
Password Authentication Tag Cloud
Earlier posts on this topic: Passwords and the average user, More on passwords, And yet more on passwords, and Practically speaking, the end is in sight for passwords.
H/T to Bruce Schneier for the link.
August 20, 2010
“C will not only let you shoot yourself in the foot, it will hand you a new magazine when you run out of bullets”
Charles Stross enumerates some of the ways “we went wrong” in the rush to today’s computing world:
According to one estimate pushed by the FBI in 2006, computer crime costs US businesses $67 billion a year. And identity fraud in the US allegedly hit $52.6Bn in 2004.
Even allowing for self-serving reporting (the FBI would obviously find it useful to inflate the threat of crime, if only to justify their budget requests), that’s a lot of money being pumped down a rat-hole. Extrapolate it worldwide and the figures are horrendous — probably nearer to $300Bn a year. To put it in perspective, it’s like the combined revenue (not profits; gross turnover) of Intel, Microsoft, Apple, and IBM — and probably a few left-overs like HP and Dell — being lost due to deliberate criminal activity.
Where does this parasitic drag come from? Where did we go wrong?
I’m compiling a little list, of architectural sins of the founders (between 1945 and 1990, more or less) that have bequeathed us the current mess. They’re fundamental design errors in our computing architectures; their emergent side-effects have permitted the current wave of computer crime to happen . . .
I make it a rule never to believe the order of magnitude claimed by a self-interested party about how much money is “lost” because of their current hobby-horse mopery and dopery. Even if the amount claimed by the FBI is off by an order of magnitude, that’s still serious money.
August 16, 2010
Practically speaking, the end is in sight for passwords
Advances in computing are not always uniformly beneficial: short passwords are increasingly vulnerable to brute-force cracking:
The availability of password-cracking tools based on increasingly powerful graphics processors means that even carefully chosen short passwords are liable to crack under a brute-force attack.
A password of less than seven characters will soon be “hopelessly inadequate” even if it contains symbols as well as alphanumerical characters, according to computer scientists at the Georgia Tech Research Institute. The security researchers recommend passwords at least 12 characters long.
The number crunching abilities of graphics processors were recently applied to commercial password auditing and recovery tools from Russian developer ElcomSoft. It’s a safe assumption that black hats are able to use the same type of technology for less laudable purposes. Richard Boyd, of the Georgia Tech Research Institute, told the BBC that the number-crunching capacity of graphics cards compares to those of supercomputers built only 10 years ago.
Passwords are going to go away, sooner rather than later. All of us have too many passwords to remember that it’s pretty much guaranteed that you’re using one of the following coping strategies:
- Using the same password on many different sites (or, shudder, all of them)
- Using a simple password (among the most commonly used are “password” and “letmein”)
- Leaving a sticky note on your monitor or your keyboard with your passwords listed
- Using the name of the site as your password for that site
There are tools available to generate passwords that avoid the most obvious pitfalls (too short, no numeric or non-alphanumeric characters, using full words), but very few people use them consistently. I don’t know what the replacement for passwords will be, but we clearly need to move to more secure ways of verifying identity as soon as we can.
August 9, 2010
IPv6 still not ready for primetime?
As you’ve probably heard, the current internet addressing system, IPv4, is running out of unallocated addresses. The replacement is called IPv6 and was supposed to be in use by now. Security concerns are holding it back:
The internet’s next-generation addressing scheme is so radically different from the current one that its adoption is likely to cause severe security headaches for those who adopt it, a researcher said last week.
With reserves of older addresses almost exhausted, the roll-out of the new scheme — known as IPv6 or Internet Protocol version 6 — is imminent. And yet, the radical overhaul still isn’t ready for prime time — in large part because IT professionals haven’t worked out a large number of security threats facing those who rely on it to route traffic over the net.
“It is extremely important for hackers to get in here fast because IPv6 is a security nightmare,” Sam Bowne, an instructor in the Computer Networking and Information Technology Department at the City College of San Francisco, said on day one of the Defcon hacker conference in Las Vegas. “We’re coming into a time of crisis and no one is ready.”
Chief among the threats is the issue of incompatible firewalls, intrusion-prevention devices, and other security appliances, Bowne said. That means many people who deploy IPv6 are forced to turn the security devices off, creating a dangerous environment that could make it easier for attackers to penetrate network fortresses.
August 6, 2010
Tide turning on porn prosecutions in the UK?
After the US government’s prosecution of a pornography company owner collapsed last month, the British anti-porn campaign has suffered a setback. The Register reports on the case:
A stunning reversal for police and prosecution in North Wales may herald the beginning of the end for controversial legislation on possession of extreme porn.
The case, scheduled to be heard yesterday in Mold Crown Court, was the culmination of a year-long nightmare for Andrew Robert Holland, of Coedpoeth, Wrexham, Clwyd as the CPS declined to offer any evidence, and he left court a free man. The saga began last summer when, following a tip-off, police raided Holland’s home looking for indecent images of children. They found none, but they did find two clips, one involving a woman purportedly having sex with a tiger, and one which is believed to have depicted sado-masochistic activity between adults.
Despite Holland’s protests that he had no interest in the material, and that it had been sent to him unsolicited “as a joke”, he was charged with possessing extreme porn. In a first court appearance in January of this year, the “tiger porn” charge was dropped when prosecuting counsel discovered the volume control and at the end of the action heard the tiger turn to camera and say: “That beats doing adverts for a living.”
The laws are seriously skewed when the potential punishment for simple possession of “extreme” pornography approaches the actual punishment for serious violent crime.
August 5, 2010
US governments still finding this “free speech” thing annoying
If you support the notion of free speech, it is most important to support it during elections . . . but not everyone feels this way:
The Associated Press reports that California’s Fair Political Practices Commission (FPPC) is considering “how to regulate new forms of political activity such as appeals on a voter’s Facebook page or in a text message.
Not whether to regulate these new forms of political speech, but how.
The recommendations apparently include “requiring tweets and texts to link to a website that includes . . . full disclosures, although some people feel the disclosure should be in the text itself no matter how brief . . . .”
To paraphrase Chief Justice John Roberts, this is why we don’t leave our free speech rights in the hands of FPPC bureaucrats. To bureaucrats like those at the FPPC, the Federal Election Commission or their analogues, there seems to be no need to show any evidence that Twitter, Facebook or text messages actually pose any threat to the public. It is enough that they these new forms of low-cost media aren’t currently regulated, but could be. Their primary concern, apparently, is that the regulation of political speech be as comprehensive as possible.
Free speech can be a messy thing — but censorship is worse.
July 26, 2010
The unwillingness to disbelieve
Mike Elgan debunks the latest “mind-crogglingly cheap computer for the masses” announcement:
“India unveils $35 computer for students,” says CNN.com. “India unveils prototype for $35 touch-screen computer,” reports BBC News. “India to provide $35 computing device to students,” says BusinessWeek.
Wow! That’s great! Too bad it will never exist. That this announcement is reported straight and without even a hint of skepticism is incomprehensible to me.
[. . .]
India itself doesn’t build touch screens. They would have to be imported from China or Taiwan. The current price for this component alone exceeds $35. Like touch screens, most solar panels are also built in China. But even the cheapest ones powerful enough to charge a tablet battery are more expensive to manufacture than $35.
Plus you need to pay for the 2GB of RAM, the case and the rest of the computer electronics. Even if you factor in Moore’s Law and assume the absolute cheapest rock-bottom junk components, a solar touch tablet with 2GB of RAM cannot be built anytime soon for less than $100.
More to the point, no country in the world can build a cheaper computer than China can. The entire tech sector in China is optimized for ultra-low-cost manufacturing. All the engineering brilliance in India can’t change that.
There’s also the point that government bureaucracies and university engineering departments are not designed for or experienced in the mass production techniques that any of these “ultra-cheap but powerful” computing initiatives all require. Have you ever heard of a government that could keep their hands (and political priorities) out of the critical decision of where this wonder device would be assembled, tested, packed, and distributed? The “industrial policy” wonks would need to get intensely involved in such a decision and the location would have to meet diverse electoral and financial requirements (note that the economics of the project won’t even make the top five priorities in the process).
Awarding the contract to just one area would be unthinkable: the benefits must be seen to be helping areas that elected the current government and emphatically not going to opposition ridings. The horsetrading over that alone would consume any possible price advantage such a scheme might have over ordinary computers and software bought commercially.
July 23, 2010
July 14, 2010
The upgrade dance
With the reminder yesterday that Microsoft has ended support for Windows XP Service Pack 2, I figured it was time to look at upgrading my computers to Windows 7. I’m not a “bleeding edge” kind of guy: I figure it’s safer to let other folks be the quality assurance department and I usually wait until the cries of pain and anguish from the first bunch of upgraders dies down before trying it myself.
I looked at the array of options (remember the days when there were only one or two flavours of operating system to worry about?) I was going to upgrade my laptop first, as it’s already been blighted with Vista, which is supposed to mean that the upgrade preserves all your installed programs and settings. I have a variety of programs I need to run, some of which are getting a bit long in the tooth, so I thought it safer to get a version of Windows 7 that offers the “Windows XP Mode” just in case some of them won’t play nice in the new OS natively. That meant I needed to buy Windows 7 Professional or Windows 7 Ultimate. The differences between those two versions was price: Ultimate offers BitLockerTM and the option of working in 35 languages, neither of which is important to me. So I picked up a copy of Windows 7 Professional.
This morning, when I tried to run the upgrade, having backed up my laptop’s hard drive, I discover that I should have bought the Ultimate version instead — because the laptop was shipped with Vista Home Premium installed, I can’t upgrade directly to Windows 7 Professional using the “preserve files and settings” option, but instead would have to re-install everything.
Well, I guess I can use this copy to upgrade the desktop, since it’ll need the full re-install everything option anyway. Drat.
Update, 15 July: Well, the actual updating part went pretty smoothly (unlike the last few times I’ve installed OSes from Microsoft), so now it’s find the programs, download updates and drivers, and get back into a working state. The longest part so far has been using the Microsoft “Windows Easy Transfer” wizard: both saving the files off the original and re-installing them on the new OS is a multi-hour exercise.
Update, 20 July: It took time, but unlike previous OS-upgrade tales of woe, this was merely time-consuming. The last of the programs I was having issues with has started to behave (although in one case it was an extremely good idea that I got the version of Windows 7 that included Windows XP Mode: my backup program hiccoughs under native Windows 7).
I can comfortably recommend the Windows 7 Easy Transfer tool: it even eased the pain of updating iTunes. I can see why some folks don’t feel the urge to move on from Vista: it “feels” very similar to Vista so far.